ESET has collaborated with the Federal Police of Brazil in an try and disrupt the Grandoreiro botnet. ESET contributed to the mission by offering technical evaluation, statistical info, and recognized command and management (C&C) server domains and IP addresses. On account of a design flaw in Grandoreiro’s community protocol, ESET researchers had been additionally in a position to get a glimpse into the victimology.
ESET automated techniques have processed tens of hundreds of Grandoreiro samples. The area technology algorithm (DGA) the malware has used since round October 2020 produces one important area, and optionally a number of failsafe domains, per day. The DGA is the one approach Grandoreiro is aware of how one can report back to a C&C server. Apart from the present date, the DGA accepts static configuration as nicely – we’ve noticed 105 such configurations as of this writing.
Grandoreiro’s operators have abused cloud suppliers equivalent to Azure and AWS to host their community infrastructure. ESET researchers supplied knowledge essential to figuring out the accounts liable for organising these servers. Additional investigation carried out by the Federal Police of Brazil led to the identification and arrest of the people in charge of these servers. On this blogpost, we have a look at how we obtained the info to help legislation enforcement to execute this disruption operation.
Background
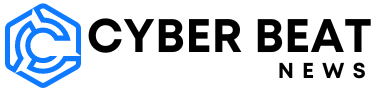
Grandoreiro is one in all many Latin American banking trojans. It has been energetic since no less than 2017 and ESET researchers have been carefully monitoring it ever since. Grandoreiro targets Brazil and Mexico, and since 2019 Spain as nicely (see Determine 1). Whereas Spain was probably the most focused nation between 2020 and 2022, in 2023 we noticed a transparent change of focus in the direction of Mexico and Argentina, the latter being new to Grandoreiro.
Performance-wise, Grandoreiro hasn’t modified very a lot since our final blogpost in 2020. We provide a short overview of the malware on this part and dive into the few adjustments, primarily new DGA logic, later.
When a Latin American banking trojan efficiently compromises a machine, it normally points an HTTP GET request to a distant server, sending some fundamental details about the compromised machine. Whereas older Grandoreiro builds applied this characteristic, over time, the builders determined to drop it.
Grandoreiro periodically displays the foreground window to seek out one which belongs to an internet browser course of. When such a window is discovered and its title matches any string from a hardcoded checklist of bank-related strings, then and solely then the malware initiates communication with its C&C server, sending requests no less than as soon as a second till terminated.
The operator has to work together manually with the compromised machine with a view to steal a sufferer’s cash. The malware permits:
- blocking the display of the sufferer,
- logging keystrokes,
- simulating mouse and keyboard exercise,
- sharing the sufferer’s display, and
- displaying faux pop-up home windows.
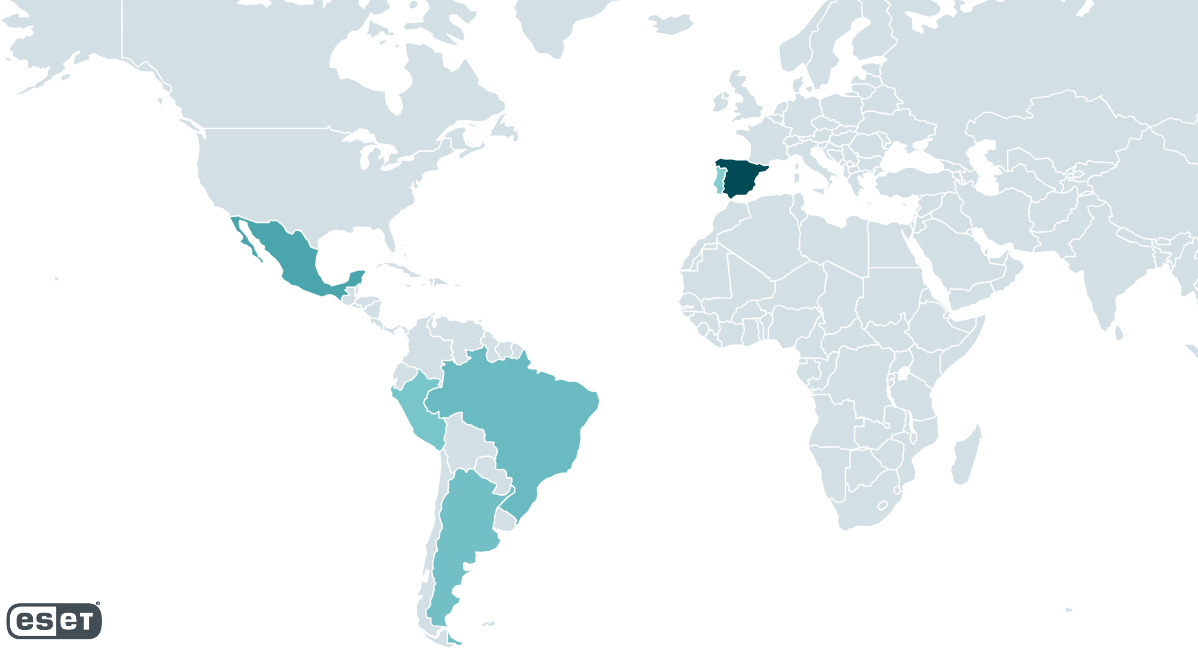
Grandoreiro undergoes fast and fixed growth. Often, we even noticed a number of new builds per week, making it tough to maintain monitor. To reveal, in February 2022, Grandoreiro’s operators added a model identifier to the binaries. In Determine 2 we present how rapidly the model identifier modified. On common, it was a brand new model each 4 days between February 2022 and June 2022. Within the month-long hole between Might 24th, 2022 and June 22nd, 2022 we continued to see new samples with progressing PE compilation instances, however they lacked the model identifier. On June 27th, 2022 the model identifier modified to V37 and we haven’t seen it change since then, leaving us to conclude that this characteristic was dropped.
Latin American banking trojans share a number of commonalities. Grandoreiro is just like different Latin American banking trojans primarily by the plain core performance and in bundling its downloaders inside MSI installers. Previously, we’ve noticed a couple of circumstances the place its downloaders had been shared with Mekotio and Vadokrist, although not within the final two years. The Grandoreiro banking trojan’s important distinction from the opposite households had been its distinctive binary padding mechanism that massively engorges the ultimate executable (described in our blogpost in 2020). Over time, Grandoreiro’s operators added this anti-analysis approach to its downloaders as nicely. To our shock, in Q3 2023, this characteristic was fully dropped from the banking trojan and downloader binaries and we haven’t noticed it since.
Since February 2022, we’ve been monitoring a second variant of Grandoreiro that differs considerably from the principle one. We noticed it, in small campaigns, in March, Might, and June 2022. Primarily based on the overwhelming majority of its C&C server domains not resolving, its core options altering very often, and its community protocol not functioning correctly, we strongly consider it’s a work in progress; therefore we’ll deal with the principle variant on this blogpost.
Grandoreiro long-term monitoring
ESET techniques designed for automated, long-term monitoring of chosen malware households have been monitoring Grandoreiro for the reason that finish of 2017, extracting model info, C&C servers, targets and, for the reason that finish of 2020, DGA configurations.
DGA monitoring
The DGA configuration is hardcoded within the Grandoreiro binary. Every configuration may be referred to by a string we name dga_id. Utilizing totally different configurations for the DGA yields totally different domains. We dive deeper into the DGA mechanism later within the textual content.
ESET has extracted a complete of 105 totally different dga_ids from the Grandoreiro samples recognized to us. 79 of those configurations no less than as soon as generated a site that resolved to an energetic C&C server IP tackle through the course of our monitoring.
The generated domains are registered through No-IP’s Dynamic DNS service (DDNS). Grandoreiro’s operators abuse the service to ceaselessly change their domains to correspond with the DGA and to alter IP addresses at will. The overwhelming majority of the IP addresses these domains resolve to are supplied by cloud suppliers, primarily AWS and Azure. Desk 1 illustrates some statistics about IP addresses used for Grandoreiro C&C servers.
Desk 1. Statistical details about Grandoreiro C&C IP addresses since we began our monitoring
| Data | Common | Minimal | Most |
| Variety of new C&C IP addresses per day | 3 | 1 | 34 |
| Variety of energetic C&C IP addresses per day | 13 | 1 | 27 |
| Lifespan of C&C IP tackle (in days) | 5 | 1 | 425 |
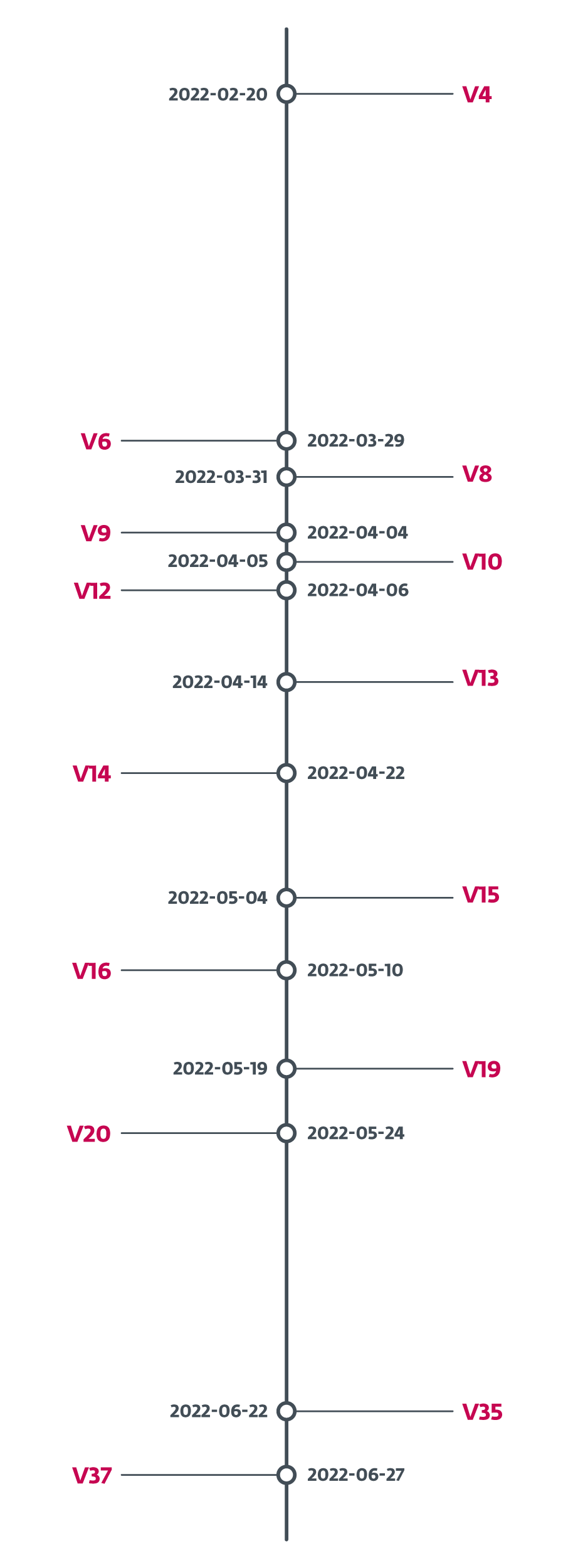
Very quickly after we started to trace the generated domains and their related IP addresses, we began to note that many domains generated by DGAs with totally different configurations resolve to the identical IP tackle (as illustrated in Determine 3). Because of this on a given day, victims compromised by Grandoreiro samples with totally different dga_id all related to the identical C&C server. This phenomenon was no coincidence – we noticed it nearly each day throughout our monitoring.
On a lot rarer events, we’ve additionally noticed an IP tackle being reused by a unique dga_id a couple of days later. Solely this time, the parameters Grandoreiro used to ascertain a connection (defined later within the textual content) modified as nicely. Because of this, within the meantime, the C&C server aspect will need to have been reinstalled or reconfigured.
Our preliminary assumption was that the dga_id is exclusive for every DGA configuration. This later proved to be incorrect – we’ve noticed two units of various configurations sharing the identical dga_id. Desk 2 reveals each of them, “jjk” and “gh”, the place “jjk” and “jjk(2)” correspond to 2 totally different DGA configurations, similar as “gh” and “gh(2)”.
Desk 2 reveals the clusters we had been in a position to observe. All DGA configurations that shared no less than one IP tackle are in the identical cluster and their related dga_ids are listed. Clusters that account for lower than 1% of all victims are disregarded.
Desk 2. Grandoreiro DGA clusters
|
Cluster ID |
dga_id checklist |
Cluster dimension |
% of all C&C servers |
% of all victims |
|
1 |
b, bbh, bbj, bbn, bhg, cfb, cm, cob, cwe, dee, dnv, dvg, dzr, E, eeo, eri, ess, fhg, fox, gh, gh(2), hjo, ika, jam, jjk, jjk(2), JKM, jpy, okay, kcy, kWn, md7, md9, MRx, mtb, n, Nkk, nsw, nuu, occ, p, PCV, pif, rfg, rox3, s, sdd, sdg, sop, tkk, twr, tyj, u, ur4, vfg, vgy, vki, wtt, ykl, Z, zaf, zhf |
62 |
93.6% |
94% |
|
2 |
jl2, jly |
2 |
2.4% |
2.5% |
|
3 |
ibr |
1 |
0.8% |
1.6% |
|
4 |
JYY |
1 |
1.6% |
1.1% |
The most important cluster incorporates 78% of all energetic dga_ids. It’s liable for 93.6% of all C&C server IP addresses and 94% of all victims we’ve seen. The one different cluster consisting of greater than 1 dga_id is cluster 2.
Some sources declare that Grandoreiro operates as malware-as-a-service (MaaS). The Grandoreiro C&C server backend doesn’t enable simultaneous exercise of a couple of operator directly. Primarily based on Desk 2, the overwhelming majority of DGA-produced IP addresses may be clustered along with no clear distribution sample. Lastly, contemplating the community protocol’s heavy bandwidth necessities (we dive into that on the finish of the blogpost), we consider that the totally different C&C servers are used as a primitive load-balancing system and that it’s extra doubtless that Grandoreiro is operated by a single group or by a couple of teams carefully cooperating with each other.
C&C monitoring
Grandoreiro’s implementation of its community protocol allowed ESET researchers to take a peek backstage and get a glimpse of the victimology. Grandoreiro C&C servers give away details about the related victims on the time of the preliminary request to every newly related sufferer. That mentioned, the info is biased by the variety of requests, their intervals, and the validity of the info supplied by the C&C servers.
Every sufferer related to the Grandoreiro C&C server is recognized by a login_string – a string Grandoreiro constructs upon establishing the connection. Totally different builds use totally different codecs and totally different codecs include totally different info. We summarize the knowledge that may be obtained from the login_string in Desk 3. The Incidence column reveals a proportion of all of the codecs we’ve seen that maintain the corresponding type of info.
Desk 3. Overview of data that may be obtained from a Grandoreiro sufferer’s login_string
|
Data |
Incidence |
Description |
|
Working system |
100% |
OS of sufferer’s machine. |
|
Pc title |
100% |
Identify of sufferer’s machine. |
|
Nation |
100% |
Nation that the Grandoreiro pattern targets (hardcoded within the malware pattern). |
|
Model |
100% |
Model (version_string) of the Grandoreiro pattern. |
|
Financial institution codename |
92% |
Codename of the financial institution that triggered the C&C connection (assigned by Grandoreiro’s builders). |
|
Uptime |
25% |
Time (in hours) that the sufferer’s machine has been operating. |
|
Display decision |
8% |
Display decision of the sufferer’s important monitor. |
|
Username |
8% |
Username of the sufferer. |
Three of the fields deserve a more in-depth rationalization. Nation is a string hardcoded within the Grandoreiro binary relatively than info obtained through acceptable companies. Due to this fact, it serves extra like an meant nation of the sufferer.
Financial institution codename is a string Grandoreiro’s builders related to a sure financial institution or different monetary establishment. The sufferer visited that financial institution’s web site, which triggered the C&C connection.
The version_string is a string figuring out a selected Grandoreiro construct. It’s hardcoded within the malware and holds a string that identifies a selected construct collection, a model (which we already talked about within the introduction), and a timestamp. Desk 4 illustrates the totally different codecs and the knowledge they maintain. Discover that among the timestamps include solely month and day, whereas others include the 12 months as nicely.
Desk 4. Record of various version_string codecs and their parsing
|
Model string |
Construct ID |
Model |
Timestamp |
|
DANILO |
DANILO |
N/A |
N/A |
|
(V37)(P1X)1207 |
P1X |
V37 |
12/07 |
|
(MX)2006 |
MX |
N/A |
20/06 |
|
fox50.28102020 |
fox50 |
N/A |
28/10/2020 |
|
MADMX(RELOAD)EMAIL2607 |
MADMX(RELOAD)EMAIL |
N/A |
26/07 |
One could also be tempted to say that the Construct ID truly identifies the operator. Nonetheless, we don’t assume that’s the case. The format of this string may be very chaotic, generally it refers solely to a month during which the binary in all probability was constructed (like (AGOSTO)2708). Moreover, we strongly consider that P1X refers to a console utilized by Grandoreiro operator(s) referred to as PIXLOGGER.
C&C server monitoring – findings
On this part, we deal with what we’ve discovered by querying the C&C servers. All of the statistical knowledge listed on this part has been obtained straight from Grandoreiro C&C servers, not from ESET telemetry.
Previous samples are nonetheless energetic
Every login_string we noticed incorporates the version_string and the overwhelming majority of these include the timestamp info (see Desk 3 and Desk 4). Whereas a number of them include solely day and month, as appears to be the developer’s selection occassionally, the oldest speaking pattern was timestamped 15/09/2020 – that’s from the time this DGA was first launched to Grandoreiro. The newest pattern was timestamped 12/23/2023.
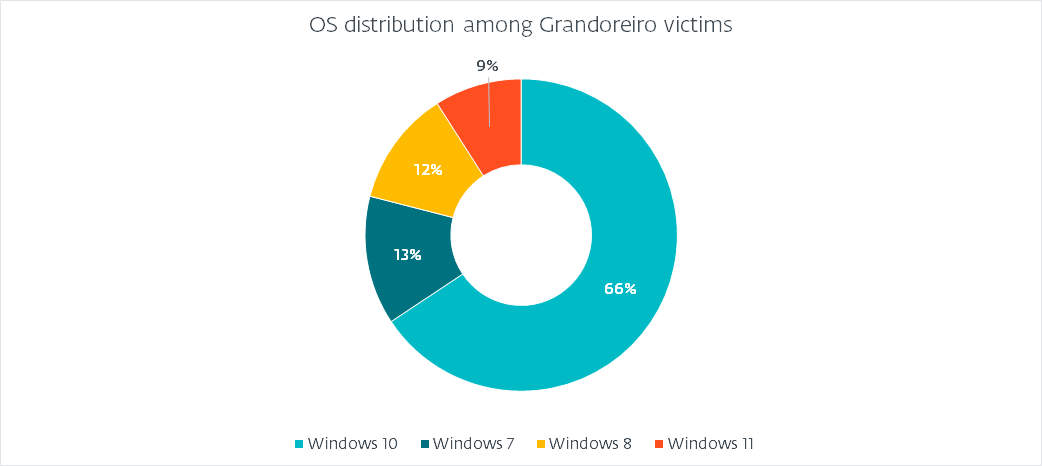
Working system distribution
Since all the login_string codecs include OS info, we will paint an correct image of what working techniques fell sufferer, as illustrated in Determine 4.
(Supposed) nation distribution
We already talked about that Grandoreiro makes use of a hardcoded worth as an alternative of querying a service to acquire the nation of the sufferer. Determine 5 reveals the distribution that we’ve noticed.
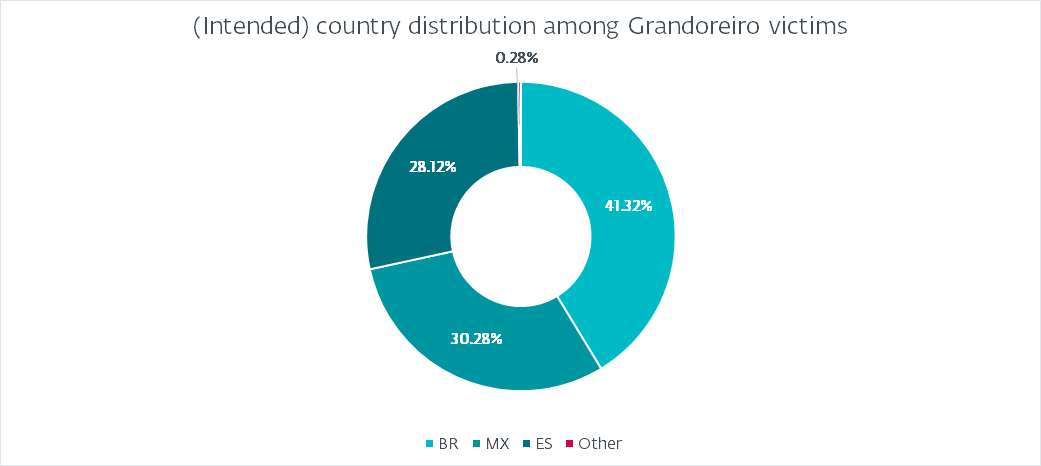
This distribution is to be anticipated of Grandoreiro. Curiously, it doesn’t correlate with the heatmap depicted in Determine 1. Essentially the most logical rationalization is that the builds should not marked correctly to resemble their meant targets. For instance, the rise in assaults in Argentina will not be mirrored in any respect by the hardcoded marking. Brazil accounts for nearly 41% of all victims, adopted by Mexico with 30% and Spain with 28%. Argentina, Portugal, and Peru account for lower than 1%. Curiously, we’ve seen a couple of (fewer than 10) victims marked as PM (Saint Pierre and Miquelon), GR (Greece), or FR (France). We consider these are both typos or produce other meanings relatively than aiming at these international locations.
Additionally observe that whereas Grandoreiro added targets from many countries outside of Latin America as early as 2020, we’ve noticed few to no campaigns concentrating on these international locations and Determine 5 helps this.
Variety of victims
We have now noticed that the typical variety of victims related in a day is 563. Nonetheless, this quantity definitely incorporates duplicates, as a result of if a sufferer stays related for a very long time, which we’ve noticed is commonly the case, then the Grandoreiro C&C server will report it on a number of requests.
Attempting to handle this concern, we outlined a distinctive sufferer as one with a novel set of figuring out traits (like pc title, username, and so on.) whereas omitting these which might be topic to alter (like uptime). With that, we ended up with 551 distinctive victims related in a day on common.
Taking into consideration that we’ve noticed victims who had been connecting to the C&C servers continually for over a 12 months’s interval, we calculated a mean variety of 114 new distinctive victims connecting to the C&C servers every day. We got here to this quantity by disregarding distinctive victims that we’ve already noticed earlier than.
Grandoreiro internals
Allow us to focus, in depth, on the 2 most important options of Grandoreiro: the DGA and the community protocol.
DGA
Grandoreiro’s operators have applied a number of sorts of DGAs through the years, with the latest one showing in July 2020. Whereas we seen a couple of minor adjustments, the core of the algorithm hasn’t change since.
The DGA makes use of a selected configuration that’s hardcoded within the binary, saved as a number of strings. Determine 6 shows one such configuration (with dga_id “bbj”), reformatted in JSON for higher readability.
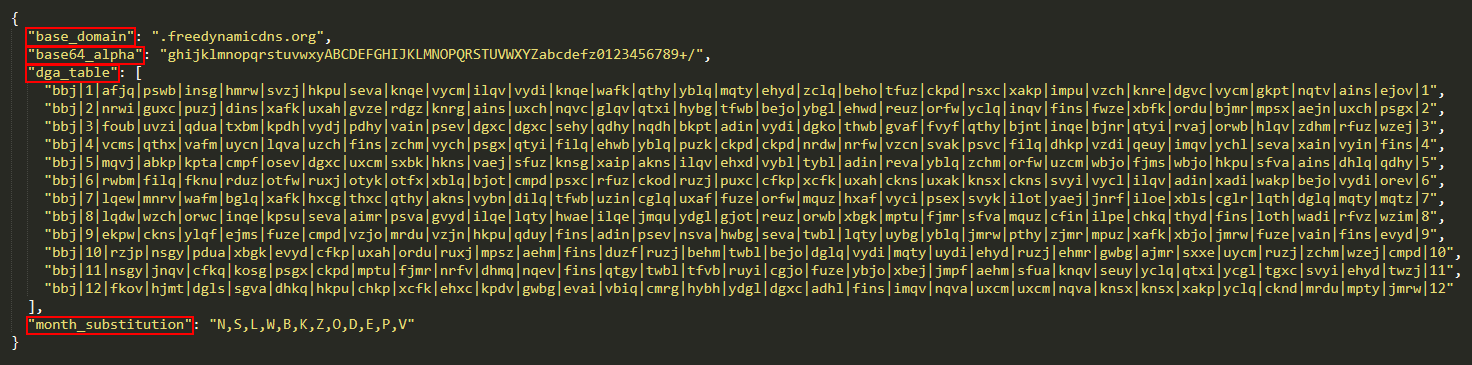
Within the overwhelming majority of circumstances, the base_domain area is freedynamicdns.org or zapto.org. As already talked about, Grandoreiro makes use of No-IP for its area registration. The base64_alpha area corresponds to the customized base64 alphabet the DGA makes use of. The month_substitution is used to substitute a month quantity for a personality.
The dga_table kinds the principle a part of the configuration. It consists of 12 strings, every with 35 fields delimited by |. The primary entry of every line is the dga_id. The second and final entry signify the month the road is meant for. The remaining 32 fields every signify a worth for a unique day of the month (leaving no less than one area unused).
The logic of the DGA is proven in Determine 7. The algorithm first selects the right line and the right entry from it, treating it as a four-byte key. It then codecs the present date right into a string and encrypts it with the important thing utilizing a easy XOR. It then prepends the dga_id to the outcome, encodes the outcome utilizing base64 with a customized alphabet, after which removes any = padding characters. The ultimate result’s the subdomain that, along with base_domain, is for use because the C&C server for the present day. The half highlighted in crimson is a failsafe mechanism and we talk about it subsequent.
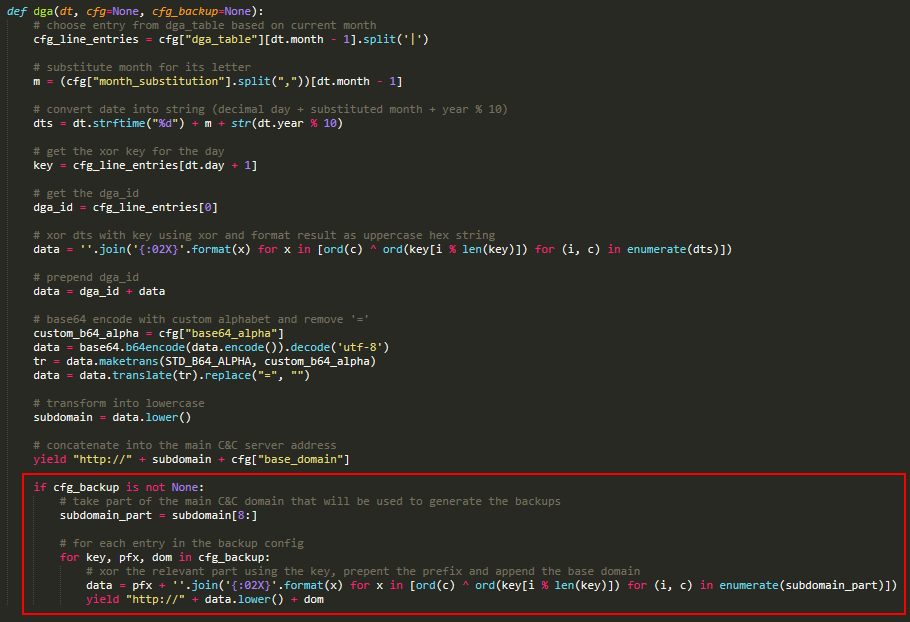
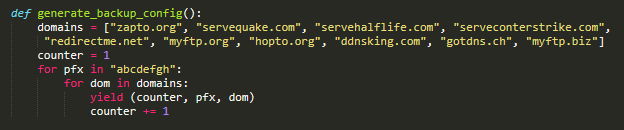
Grandoreiro has applied, in some builds, a failsafe mechanism for when the principle area fails to resolve. This mechanism will not be current in all builds and its logic has modified a couple of instances, however the fundamental concept is illustrated in Determine 7. It makes use of a configuration that’s fixed within the samples we analyzed and may be generated by the straightforward code proven in Determine 8. Every entry consists of a key, a prefix, and a base area.
The failsafe algorithm takes part of the principle C&C subdomain. It then iterates over all configuration entries, encrypts it utilizing XOR and prepends a prefix, just like the principle algorithm half.
Since September 2022, we’ve began to watch samples that make the most of a barely modified DGA. The algorithm stays nearly equivalent, however relatively than base64 encoding the subdomain within the closing step, a hardcoded prefix is prepended to it. Primarily based on our monitoring, this technique has grow to be the dominant one since roughly July 2023.
Community protocol
Grandoreiro makes use of RTC Portal, a set of Delphi parts constructed on high of the RealThinClient SDK which is constructed on high of HTTP(S). The RTC Portal was discontinued in 2017 and its supply code printed on GitHub. Primarily, RTC Portal permits a number of Controls to remotely entry a number of Hosts. Hosts and Controls are separated by a mediator part referred to as Gateway.
Grandoreiro operators use a console (performing because the Management) to connect with the C&C server (performing as Gateway) and to speak with the compromised machines (performing as Hosts). To connect with Gateway, three parameters are required: a secret key, the important thing size, and a login.
The key secret’s used to encrypt the preliminary request despatched to the server. Due to this fact, the server additionally must know the key key in order to decrypt the preliminary shopper request.
The important thing size determines the size of the keys to encrypt the visitors, established through the handshake. The visitors is encrypted utilizing a customized stream cipher. Two totally different keys are established – one for inbound and one for outbound visitors.
The login may be any string. The Gateway requires every related part to have a novel login.
Grandoreiro makes use of two totally different combos of secret key and key size values, all the time hardcoded within the binary, and we already mentioned the login_string that’s used because the login.
The RTC documentation states that it may solely deal with a restricted variety of connections directly. Contemplating that every related Host must ship no less than one request per second or else its connection is dropped, we consider that the explanation Grandoreiro makes use of a number of C&C servers is an try to not overwhelm any one in all them.
Conclusion
On this blogpost, we’ve supplied a peek backstage of our long-term monitoring of Grandoreiro that helped to make this disruption operation attainable. We have now described in depth how Grandoreiro’s DGA works, what number of totally different configurations exist concurrently, and the way we had been in a position to spot many IP tackle overlaps amongst them.
We have now additionally supplied statistical info obtained from the C&C servers. This info offers a wonderful overview of the victimology and concentrating on, whereas additionally permitting us to see the precise degree of affect.
The disruption operation led by the Federal Police of Brazil geared toward people who’re believed to be excessive up within the Grandoreiro operation hierarchy. ESET will proceed to trace different Latin American banking trojans whereas carefully monitoring for any Grandoreiro exercise following this disruption operation.
For any inquiries about our analysis printed on WeLiveSecurity, please contact us at threatintel@eset.com.
ESET Analysis presents non-public APT intelligence studies and knowledge feeds. For any inquiries about this service, go to the ESET Threat Intelligence web page.
IoCs
Information
|
SHA-1 |
Filename |
Detection |
Description |
|
FB32344292AB36080F2D040294F17D39F8B4F3A8 |
Notif.FEL.RHKVYIIPFVBCGQJPOQÃ.msi |
Win32/Spy.Grandoreiro.DB |
MSI downloader |
|
08C7453BD36DE1B9E0D921D45AEF6D393659FDF5 |
RYCB79H7B-7DVH76Y3-67DVHC6T20-CH377DFHVO-6264704.msi |
Win32/Spy.Grandoreiro.DB |
MSI downloader |
|
A99A72D323AB5911ADA7762FBC725665AE01FDF9 |
pcre.dll |
Win32/Spy.Grandoreiro.BM |
Grandoreiro |
|
4CDF7883C8A0A83EB381E935CD95A288505AA8B8 |
iconv.dll |
Win32/Spy.Grandoreiro.BM |
Grandoreiro (with binary padding) |
Community
|
IP |
Area |
Internet hosting supplier |
First seen |
Particulars |
|
20.237.166[.]161 |
DGA‑generated |
Azure |
2024‑01‑12 |
C&C server. |
|
20.120.249[.]43 |
DGA‑generated |
Azure |
2024‑01‑16 |
C&C server. |
|
52.161.154[.]239 |
DGA‑generated |
Azure |
2024‑01‑18 |
C&C server. |
|
167.114.138[.]249 |
DGA‑generated |
OVH |
2024‑01‑02 |
C&C server. |
|
66.70.160[.]251 |
DGA‑generated |
OVH |
2024‑01‑05 |
C&C server. |
|
167.114.4[.]175 |
DGA‑generated |
OVH |
2024‑01‑09 |
C&C server. |
|
18.215.238[.]53 |
DGA‑generated |
AWS |
2024‑01‑03 |
C&C server. |
|
54.219.169[.]167 |
DGA‑generated |
AWS |
2024‑01‑09 |
C&C server. |
|
3.144.135[.]247 |
DGA‑generated |
AWS |
2024‑01‑12 |
C&C server. |
|
77.246.96[.]204 |
DGA‑generated |
VDSina |
2024‑01‑11 |
C&C server. |
|
185.228.72[.]38 |
DGA‑generated |
Grasp da Net |
2024‑01‑02 |
C&C server. |
|
62.84.100[.]225 |
N/A |
VDSina |
2024‑01‑18 |
Distribution server. |
|
20.151.89[.]252 |
N/A |
Azure |
2024‑01‑10 |
Distribution server. |
MITRE ATT&CK methods
This desk was constructed utilizing version 14 of the MITRE ATT&CK framework.
|
Tactic |
ID |
Identify |
Description |
|
Useful resource Growth |
Develop Capabilities: Malware |
Grandoreiro builders develop their very own customized downloaders. |
|
|
Preliminary Entry |
Phishing |
Grandoreiro spreads by means of phishing emails. |
|
|
Execution |
Person Execution: Malicious File |
Grandoreiro pressures victims to manually execute the phishing attachment. |
|
|
Persistence |
Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder |
Grandoreiro makes use of the usual Autostart areas for persistence. |
|
|
Hijack Execution Circulate: DLL Search Order Hijacking |
Grandoreiro is executed by compromising the DLL search order. |
||
|
Protection Evasion |
Deobfuscate/Decode Information or Data |
Grandoreiro is commonly distributed in password-protected ZIP archives. |
|
|
Obfuscated Information or Data: Binary Padding |
Grandoreiro EXEs used to have enlarged .rsrc sections with massive BMP photos. |
||
|
System Binary Proxy Execution: Msiexec |
Grandoreiro downloaders are bundled inside MSI installers. |
||
|
Modify Registry |
Grandoreiro shops a part of its configuration knowledge within the Home windows registry. |
||
|
Discovery |
Utility Window Discovery |
Grandoreiro discovers on-line banking web sites based mostly on window names. |
|
|
Course of Discovery |
Grandoreiro discovers safety instruments based mostly on course of names. |
||
|
Software program Discovery: Safety Software program Discovery |
Grandoreiro detects the presence of banking safety merchandise. |
||
|
System Data Discovery |
Grandoreiro collects details about the sufferer’s machine, equivalent to %COMPUTERNAME% and working system. |
||
|
Assortment |
Enter Seize: GUI Enter Seize |
Grandoreiro can show faux pop-ups and seize textual content typed into them. |
|
|
Enter Seize: Keylogging |
Grandoreiro is able to capturing keystrokes. |
||
|
Electronic mail Assortment: Native Electronic mail Assortment |
Grandoreiro’s operators developed a instrument to extract electronic mail addresses from Outlook. |
||
|
Command and Management |
Information Encoding: Non-Customary Encoding |
Grandoreiro makes use of RTC, which encrypts knowledge with a customized stream cipher. |
|
|
Dynamic Decision: Area Era Algorithms |
Grandoreiro depends solely on DGA to acquire C&C server addresses. |
||
|
Encrypted Channel: Symmetric Cryptography |
In RTC, encryption and decryption are achieved utilizing the identical key. |
||
|
Non-Customary Port |
Grandoreiro usually makes use of non-standard ports for distribution. |
||
|
Utility Layer Protocol |
RTC is constructed on high of HTTP(S). |
||
|
Exfiltration |
Exfiltration Over C2 Channel |
Grandoreiro exfiltrates knowledge to its C&C server. |
|
|
Influence |
System Shutdown/Reboot |
Grandoreiro can pressure a system reboot. |